A common use case of API Gateway is building API endpoints in top of Lambda functions. It can also be used as an API proxy to connect to AWS services. In this guide, I will walk you through how to create your own API using API Gateway and DynamoDB only and go through advanced features to enhance your API endpoints such as:
- Mapping templates, Integration Request and Integration Response.
- Error handling and request validation.
- Authentication with AWS Cognito and Lambda Authorizer.
- API Throttling with Plan usage and API keys.
- API documentation generation.
- API Gateway custom domain.
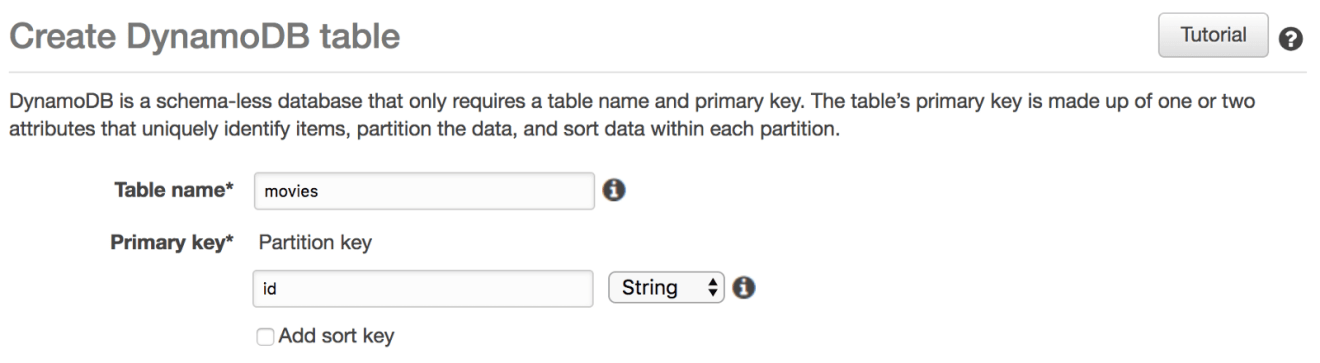
Setting up DynamoDB
To get started, create a DynamoDB table called movies with an id as a partition key (leave the read/write capacity to default values):
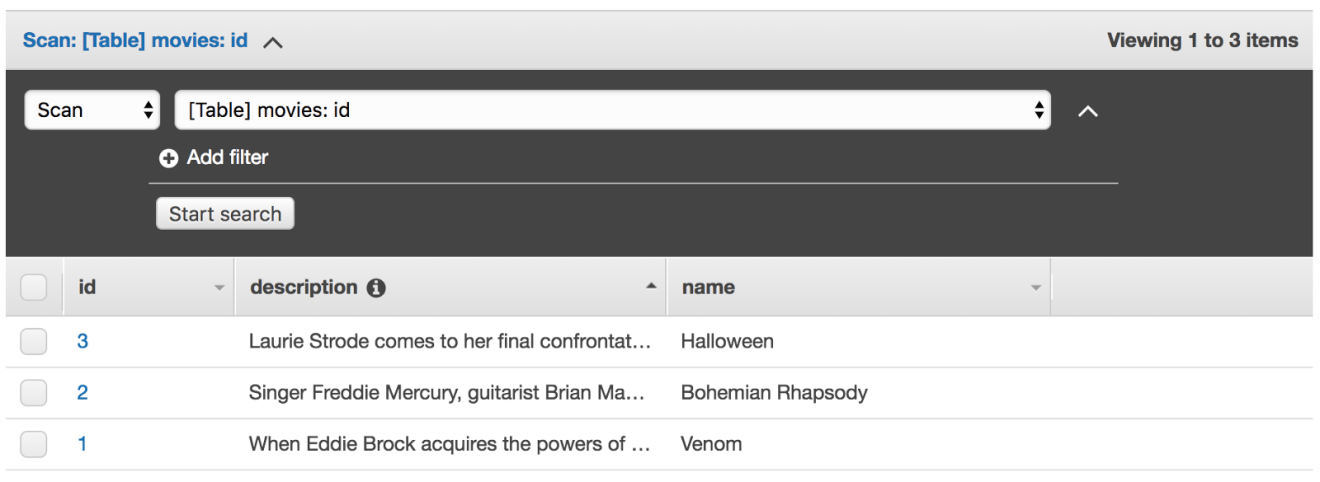
Next, insert few items into the table, it should look something like this:
Next, we need to grant the API Gateway access to DynamoDB table. Therefore we need to create an IAM role assumable by API Gateway:
1 | { |
The role will give API Gateway permission to invoke the following DynamoDB operations on movies table:
1 | { |
API Endpoints
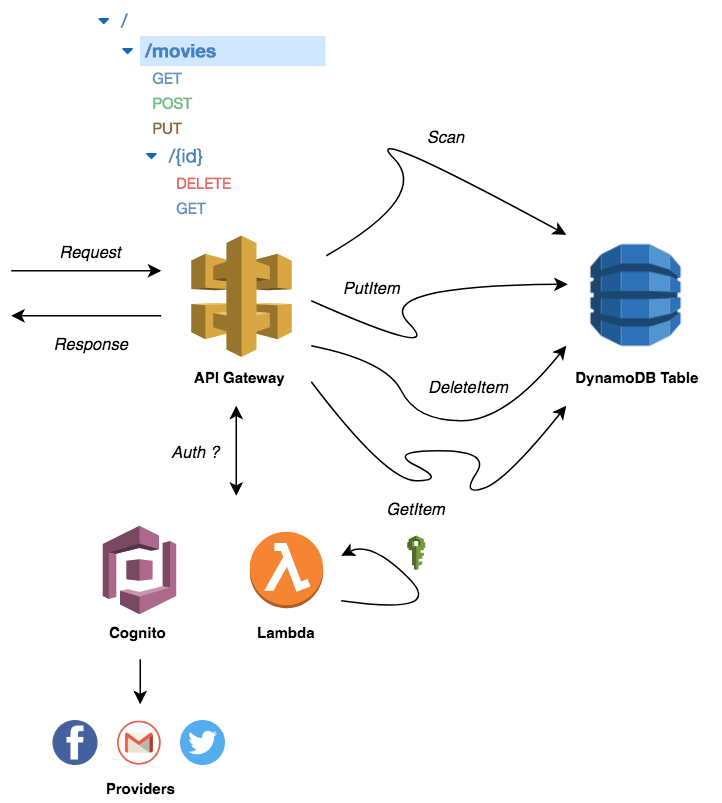
Before going into further detail about the architecture, the following diagram shows how API Gateway and DynamoDB will fit into the API architecture:
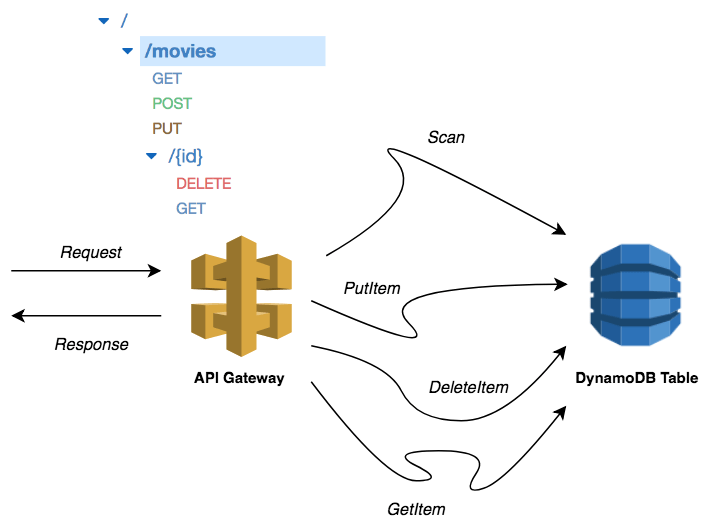
When calling the API endpoints, the request will go through the API Gateway, which will invoke the appropriate DynamoDB operation. This returns a response which is proxied by the API Gateway to the client in a JSON format.
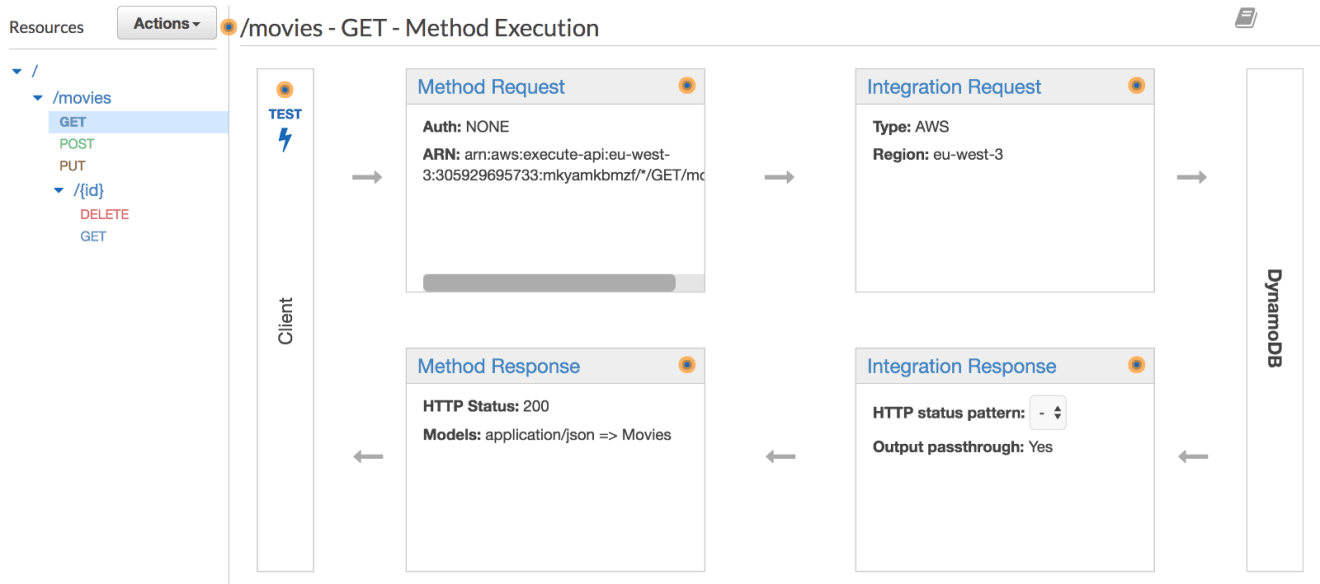
GET /MOVIES
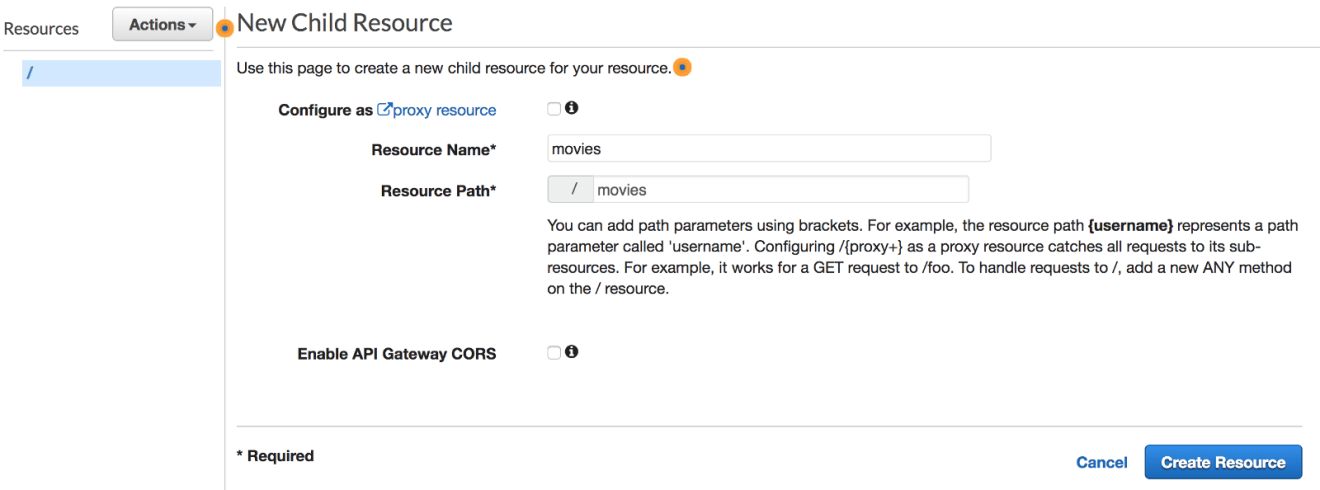
Create new API called MoviesAPI from API Gateway Console, and create a new resource, let’s call it movies:
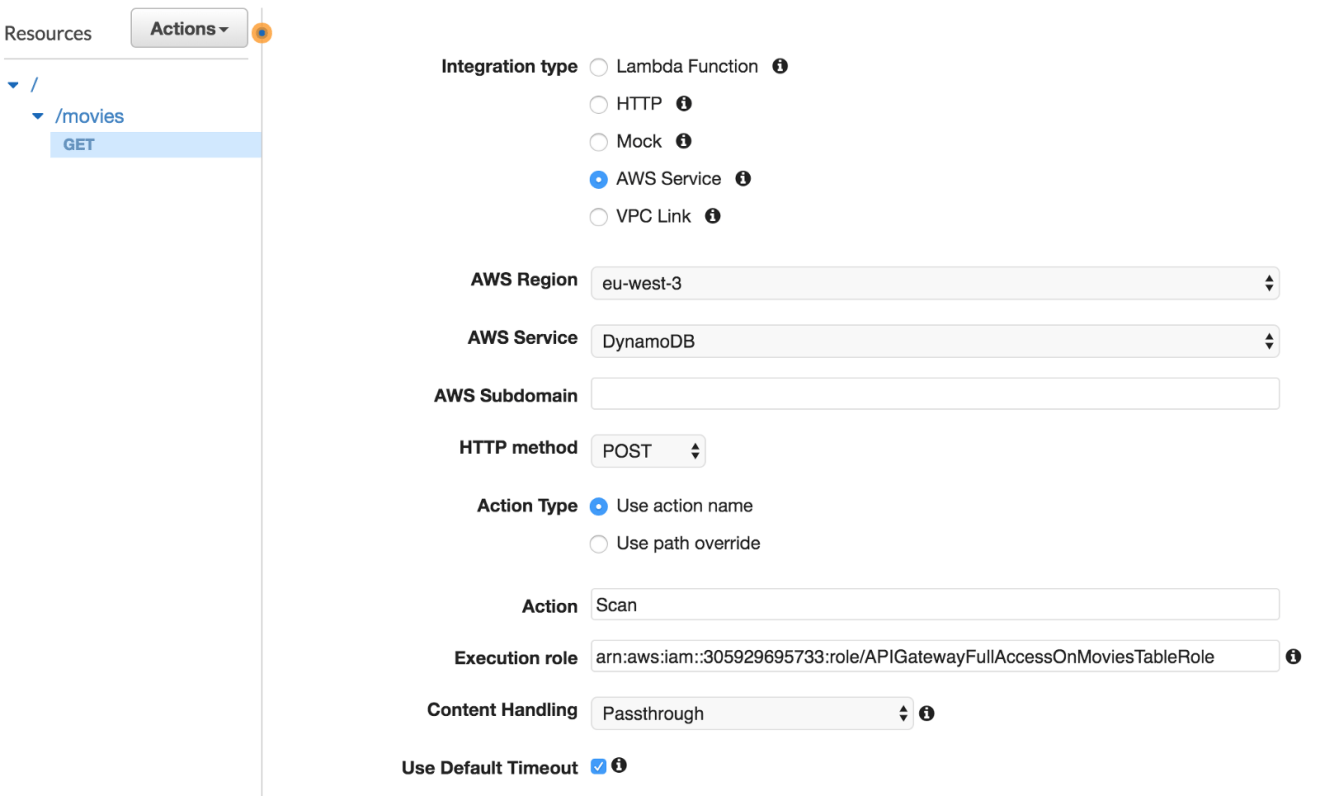
Expose a GET method on /movies resource by clicking on “Create Method”. Select AWS Service under the “Integration type” section, choose the DynamoDB service, set the HTTP method to be POST and action type to be a Scan operation.
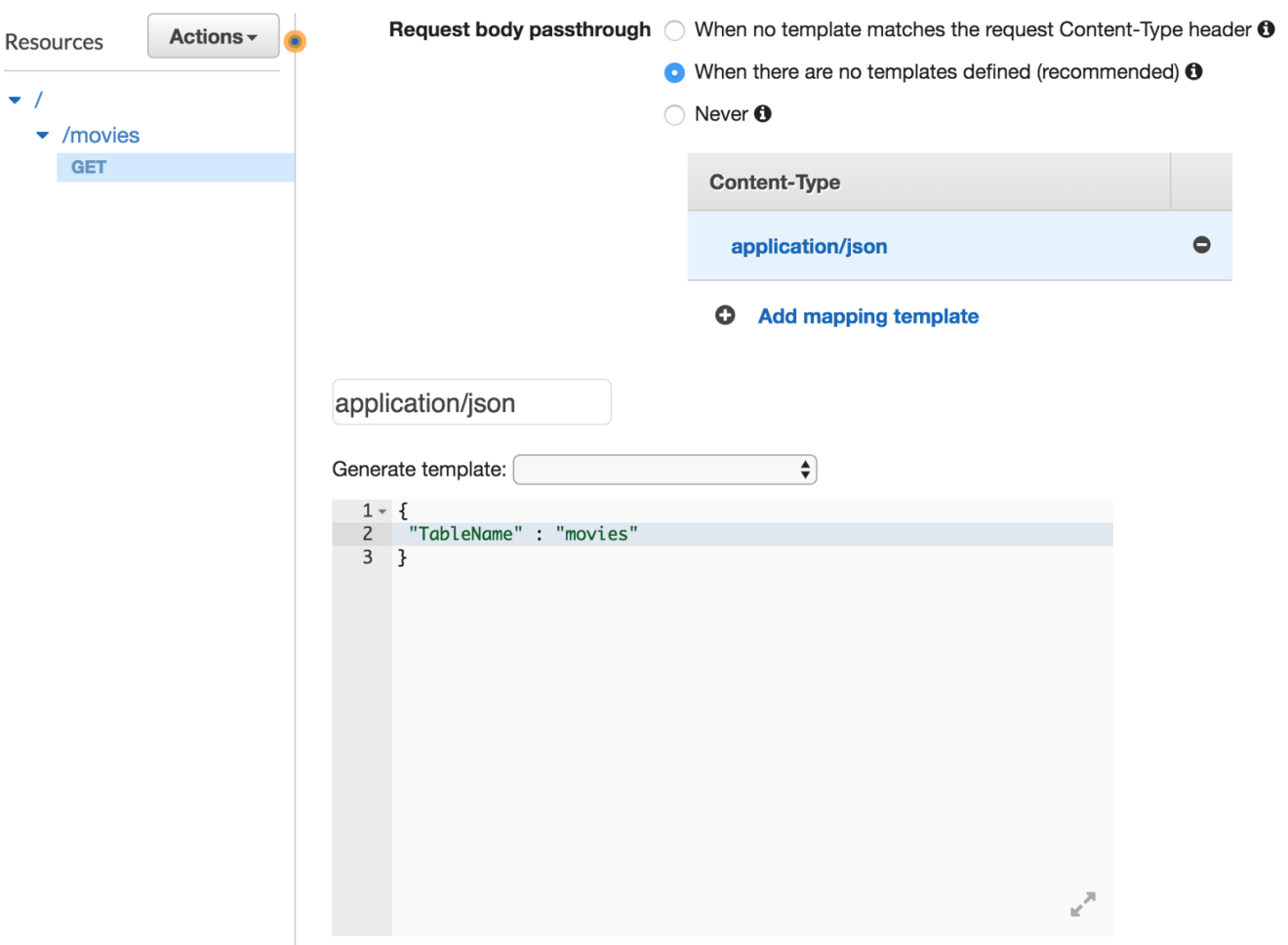
Next, we need to transform the HTTP request coming into API Gateway to a proper Scan request for DynamoDB. In the API Gateway console, select the “Integration Request”. All the way at the bottom we can select the Body Mapping Templates. Here, create a new application/json mapping template with the following configuration:
Deploy the API from “Actions” and create a new deployment stage, an invocation URL will be displayed:
Point your browser to the URL given or use a modern REST client like Postman. The endpoint will return a list of movies in a JSON format:
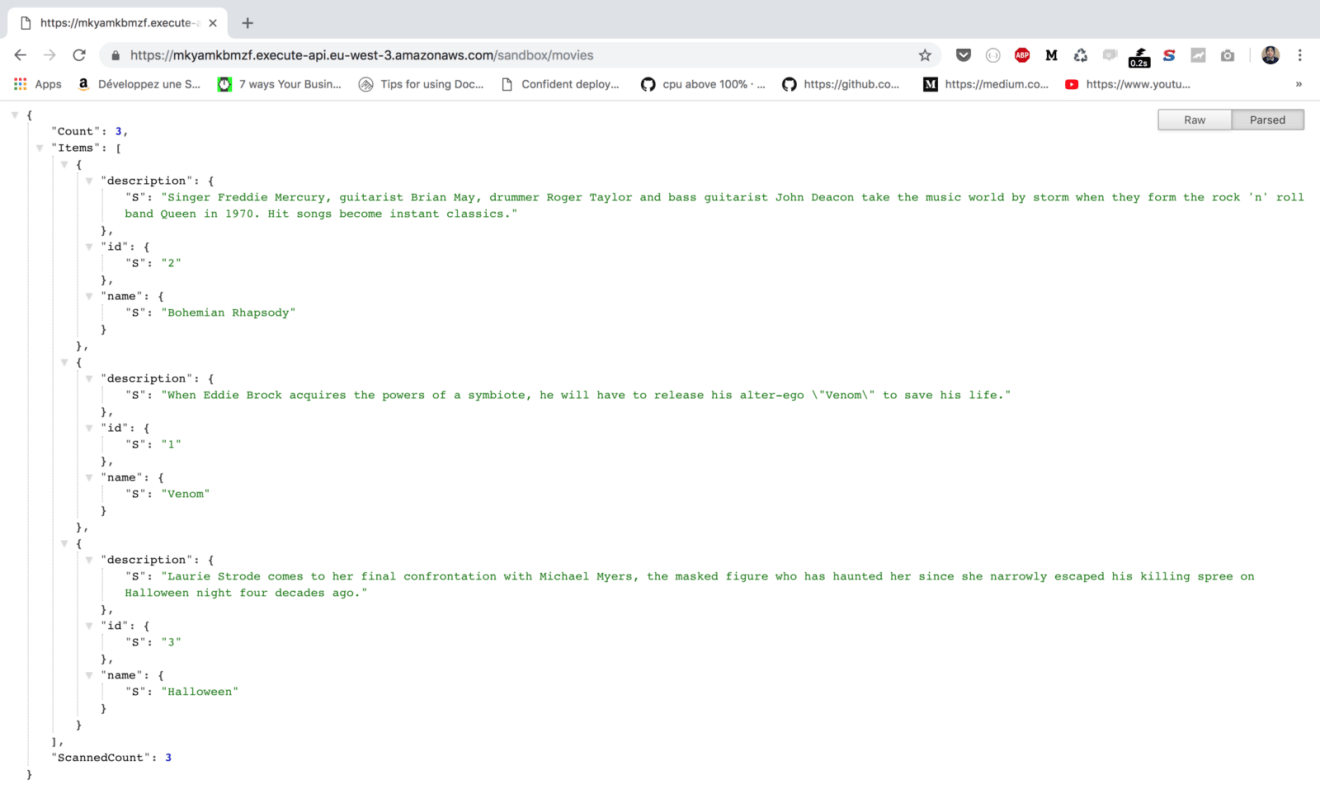
The output is returned in DynamoDB response format, in order to map the raw response to traditional JSON object structure, we will use Integration Response feature.
Click on “GET” method and navigate to “Integration Response”, expand the 200 response code. Expand the “Mapping Templates” section. In Content-Type choose application/json and create a mapping template that loop through each item from the Items array, extracts the relevant attributes of the movie’s item and places them into a response structure:
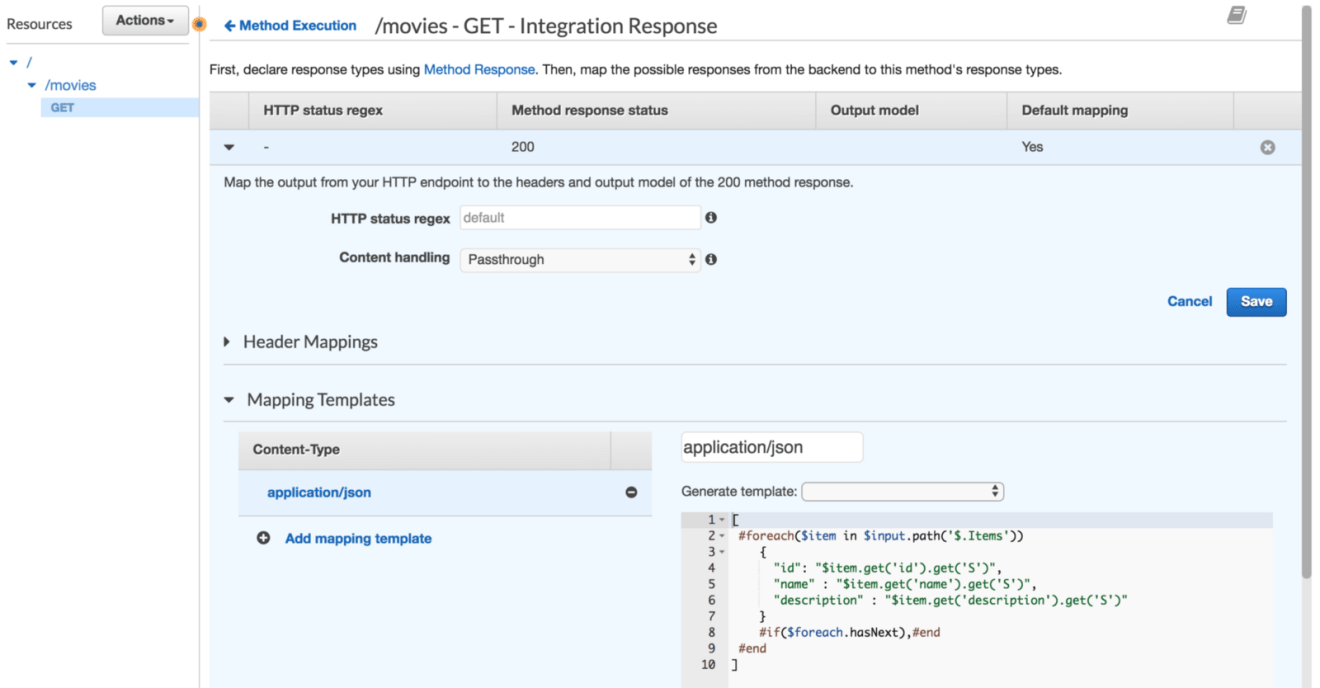
Mapping template is a script expressed in Velocity Template Language (VTL) and applied to the payload using JSONPath expressions.
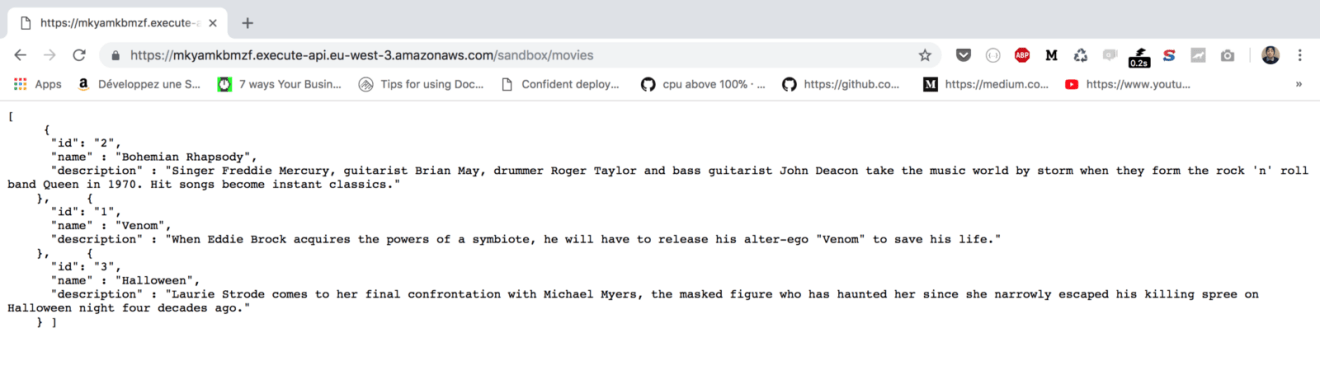
As a result, you should now see a formatted response.
GET /MOVIES/:ID
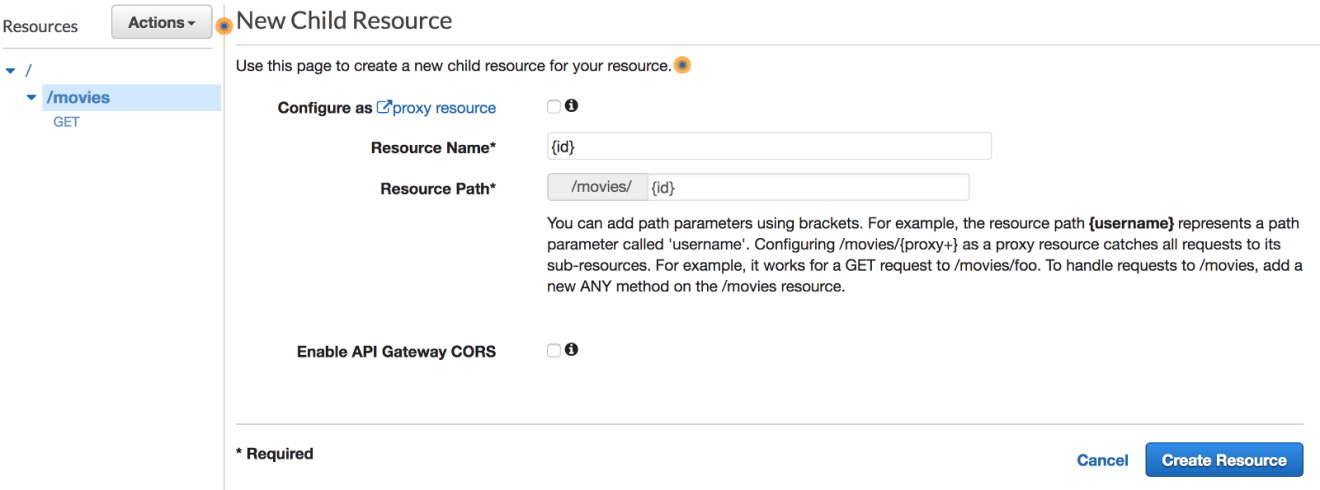
The second endpoint will be responsible of fetching a movie based on an ID provided by the client. Hence, a new resource with a path parameter should be created. The value of ID will be made available via the $input.params(‘id’) method:
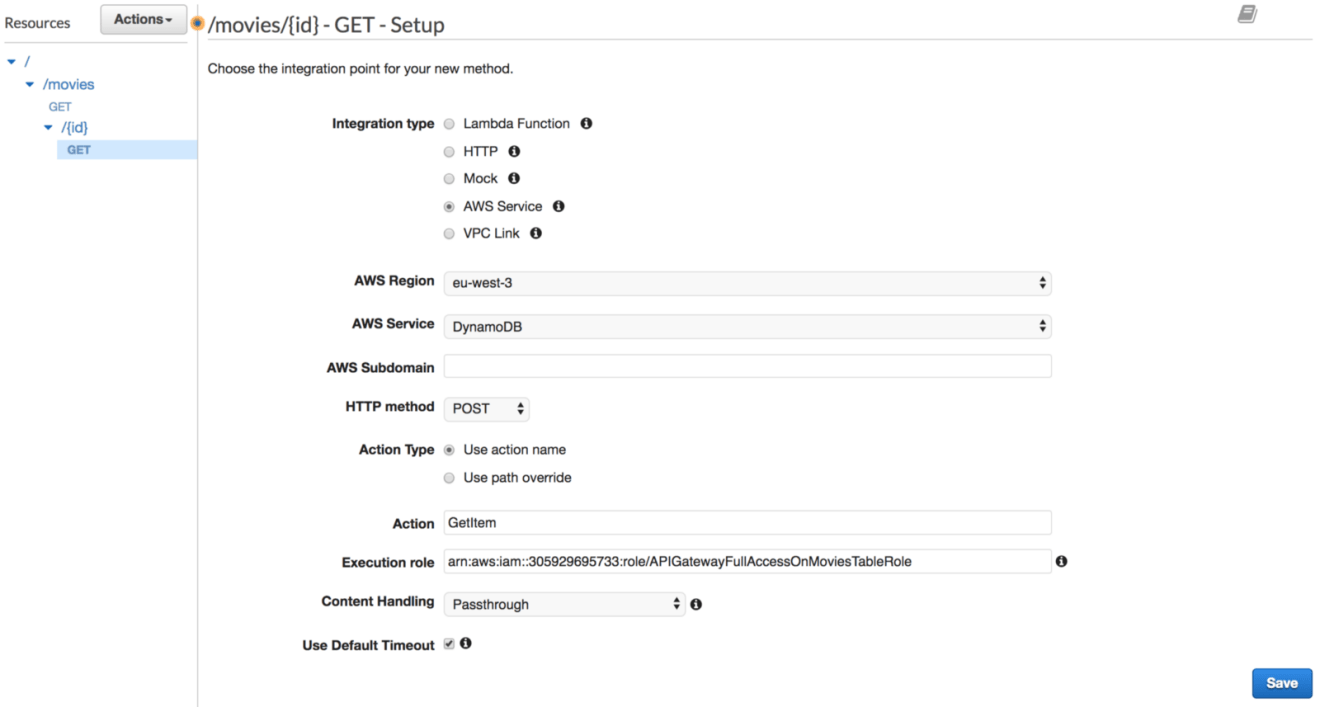
Expose a GET method, and then link the resource to the DynamoDB service. The action will be GetItem operation:
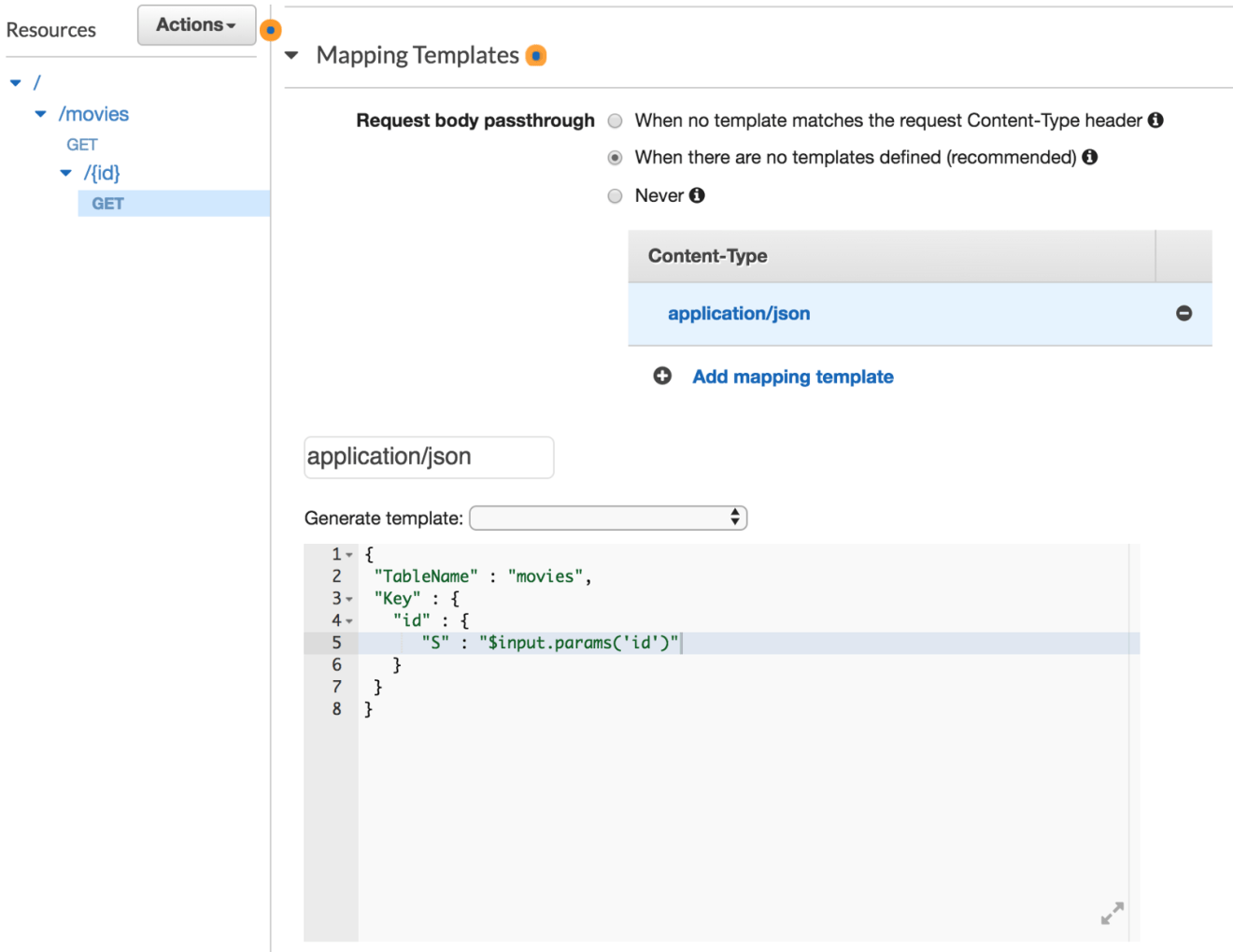
Again, specify a body mapping template for the integration request, now with the following template:
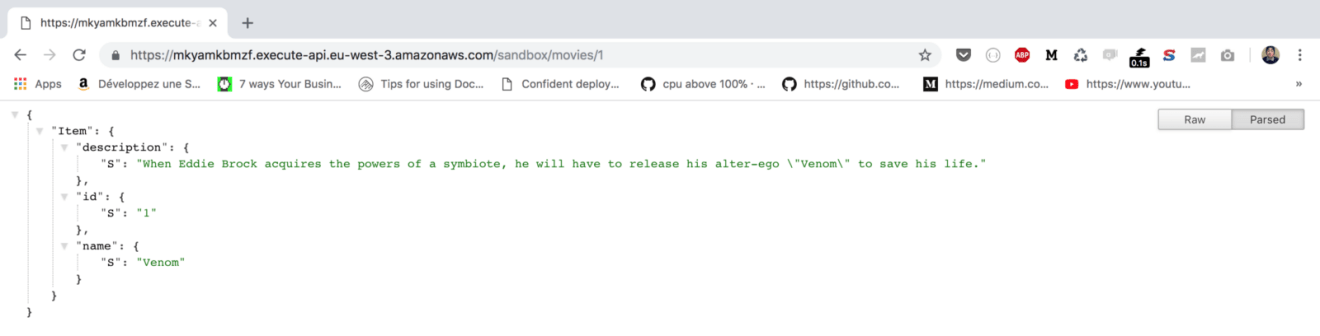
When the API URL is invoked with an ID, the movie corresponding to the ID is returned if it exists.
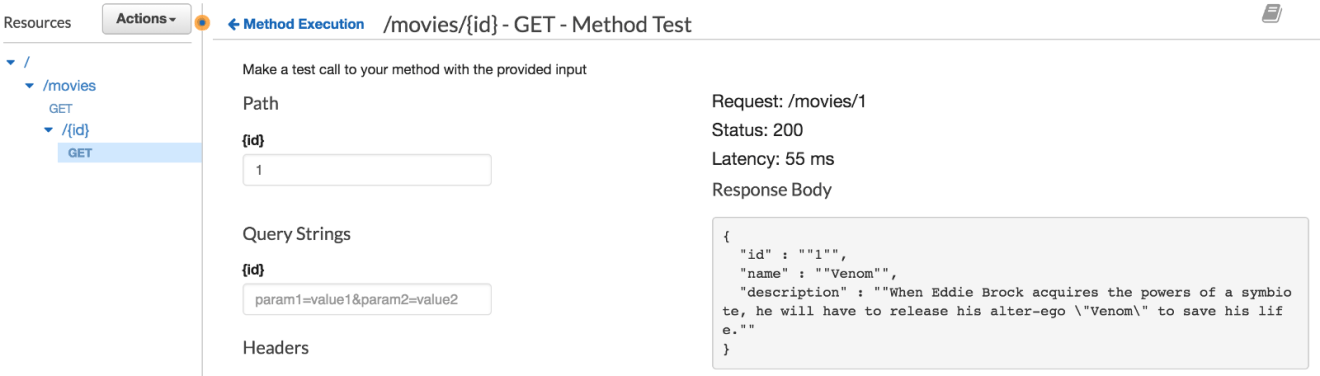
Similarly we will use integration response to map the raw DynamoDB response to the similar JSON object structure we defined earlier:
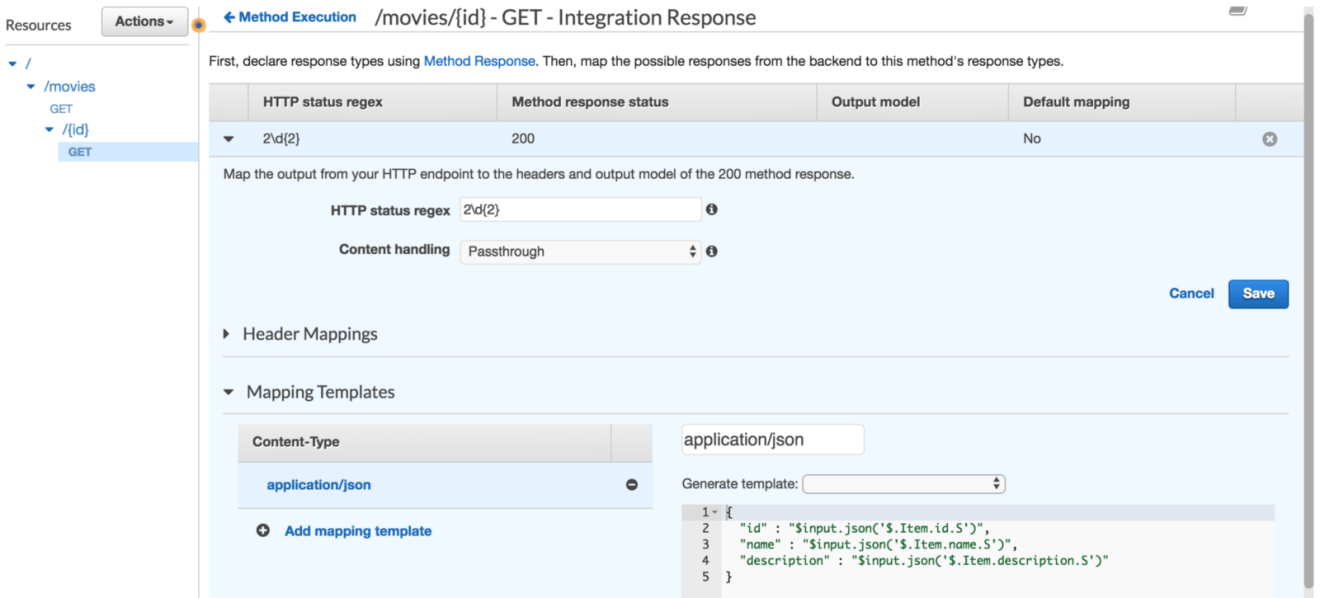
If you test it out once again, the following JSON will be returned:
POST /MOVIES
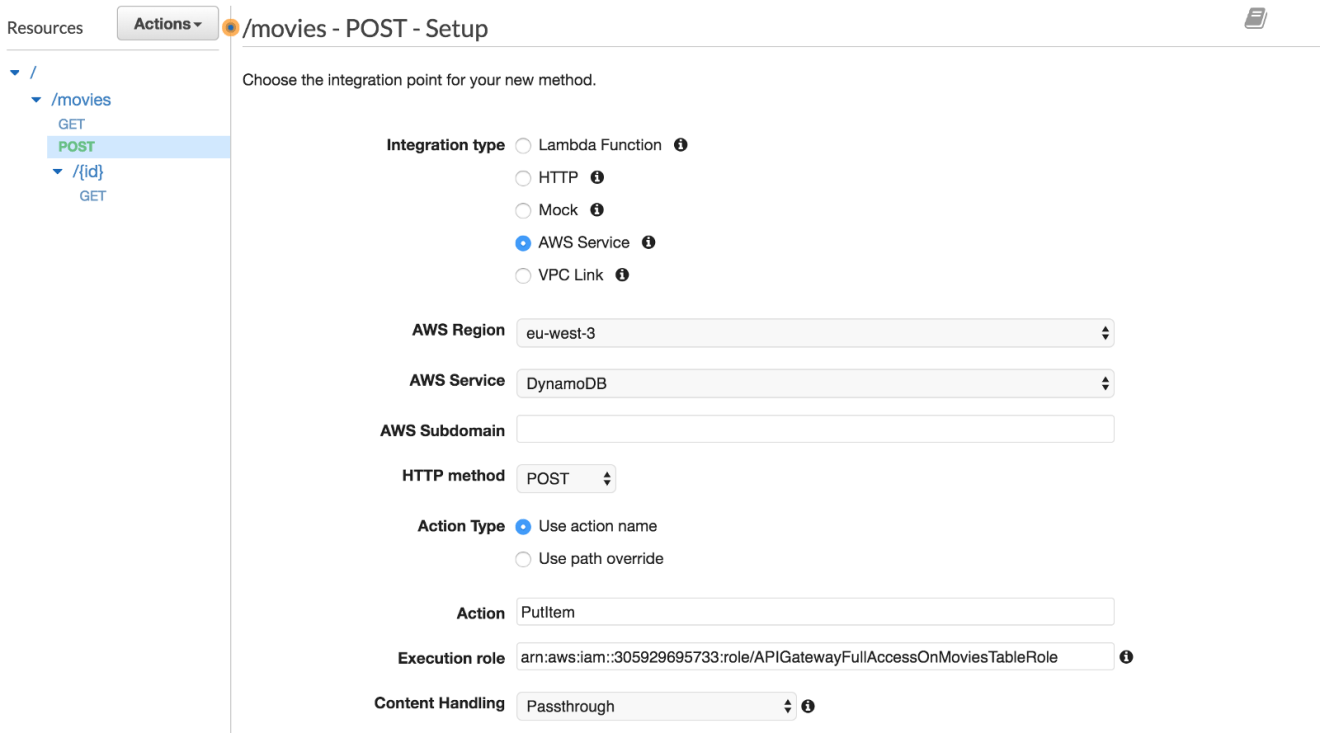
Now we know how the GET method works with and without path parameters. The next step will be to insert a new item to the table. Create a POST method with PutItem as an action:
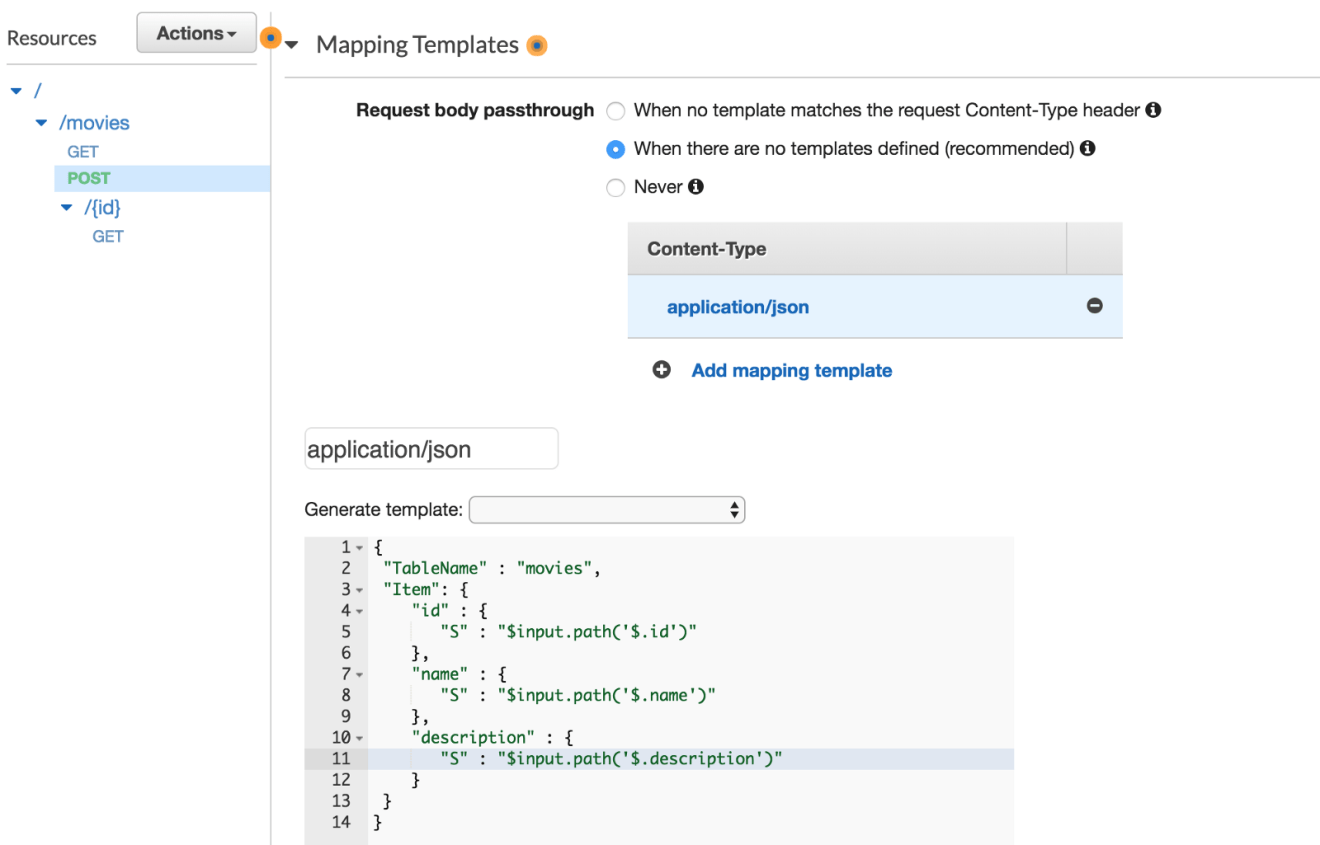
We will create a mapping template to transform the client request into the structure that the DynamoDB API PutItem requires. The below mapping template creates the JSON structure required by the DynamoDB PutItem API. The three input variables are referenced from the request JSON using the $input variable:
Back in the “Method Execution” pane click “TEST”. Create an example request body that matches the API definition documented above and then choose “Test”. For example, your request body could be:
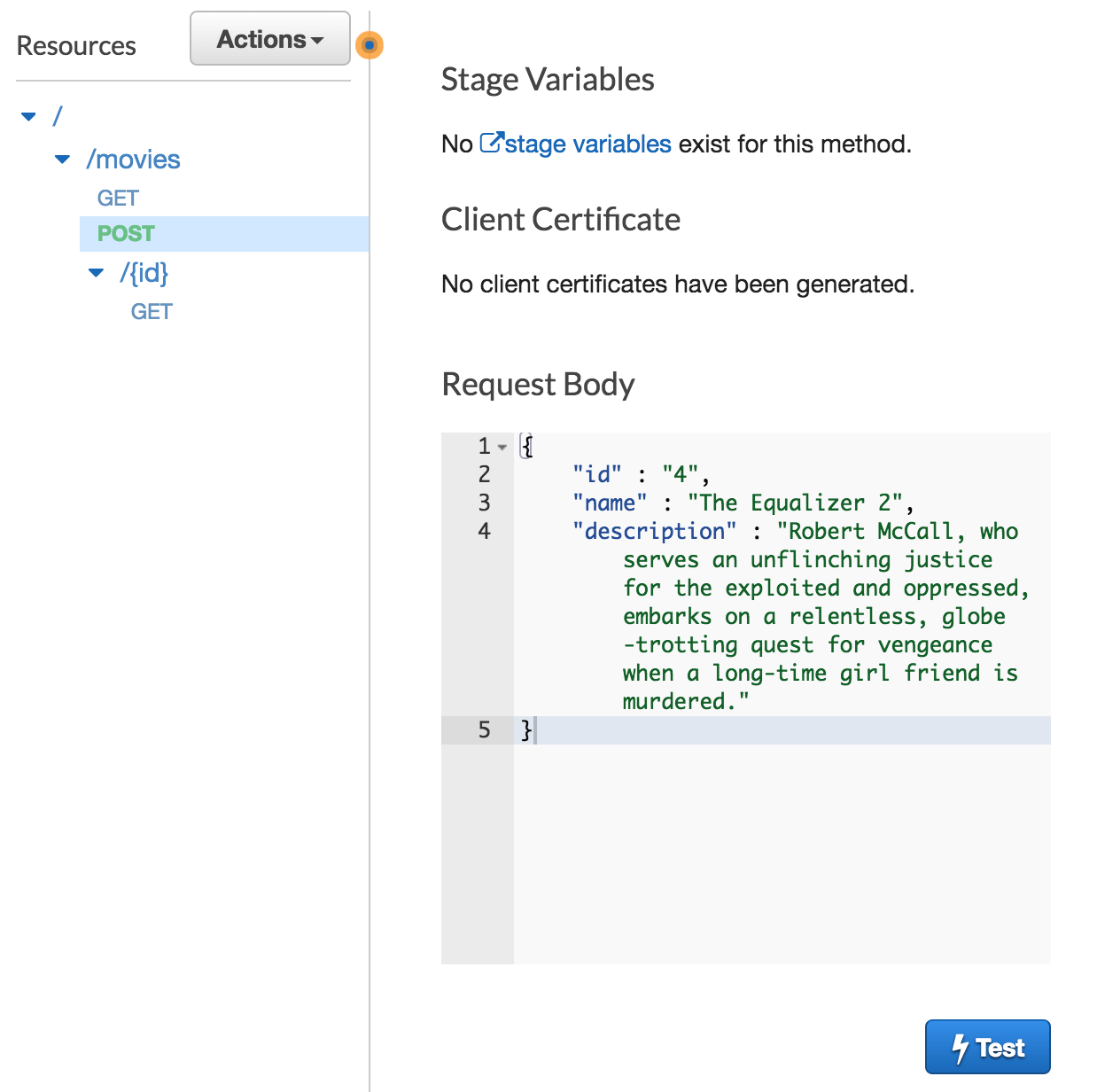
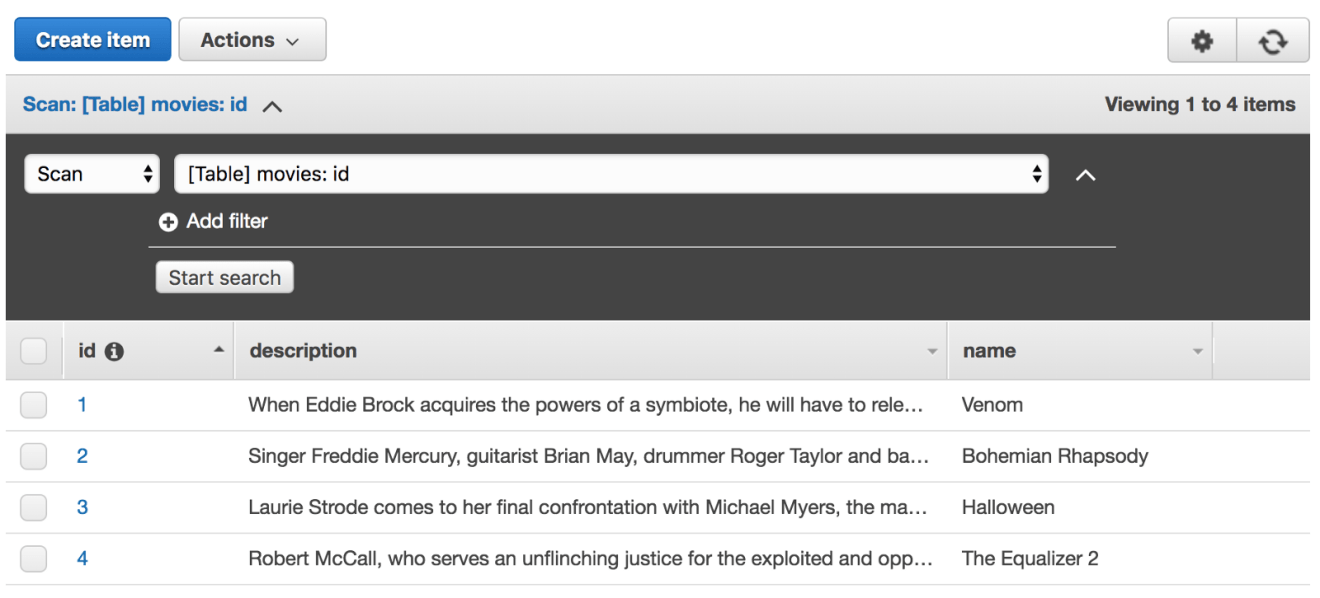
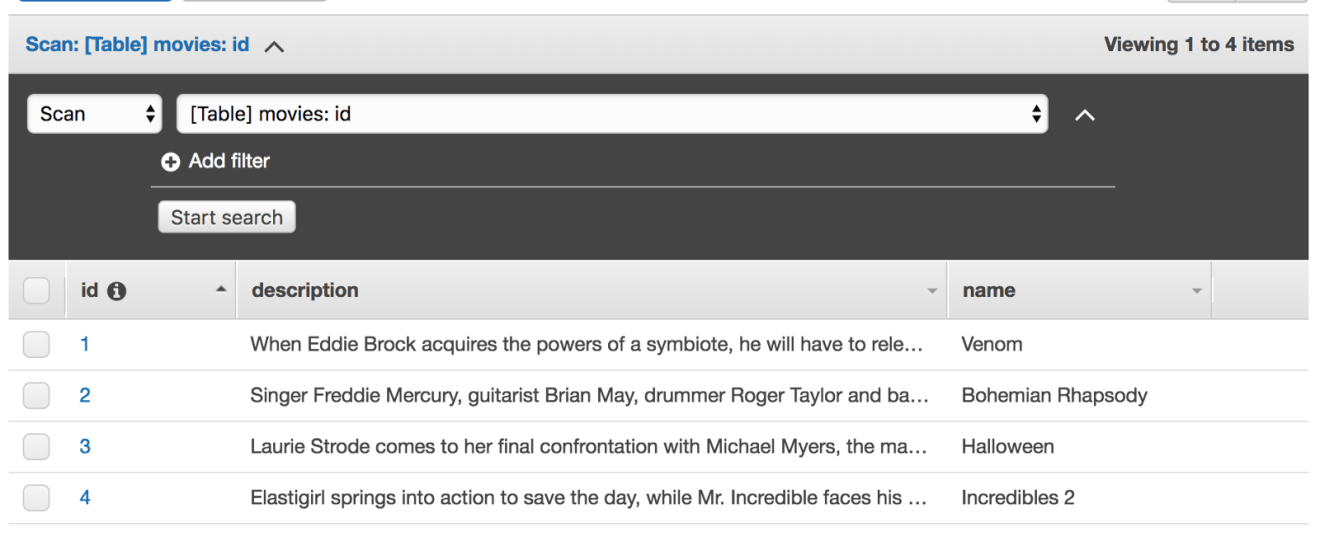
Navigate to the DynamoDB console and view the movies table to show that the request really was successfully processed:
Try to insert a new movie without giving a movie’s name attribute. The following error will returned:
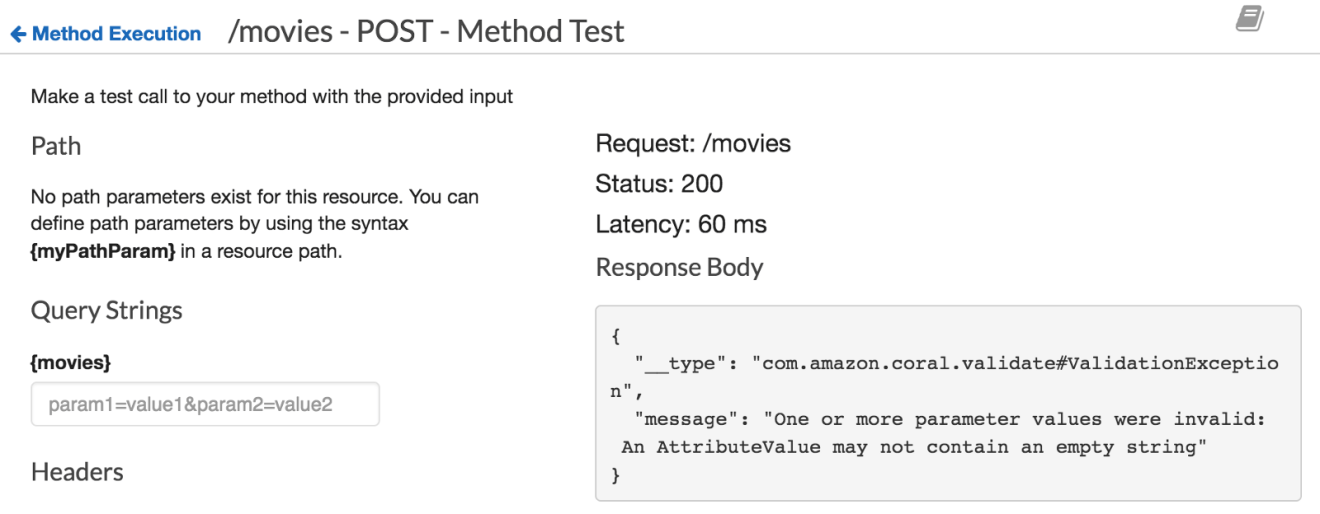
It’s a DynamoDB PutItem error. Fortuently, API Gateway allows you to validate your request body before invoking the downstream resources (In our example the DynamoDB table). To achieve this, we will use API Gateway Models. A Model defines the payload data structure. Models definitions are written using JSON Schema draft 4.
In the API Gateway, navigate to the Models tab and create a new model. Fill in the form as so:
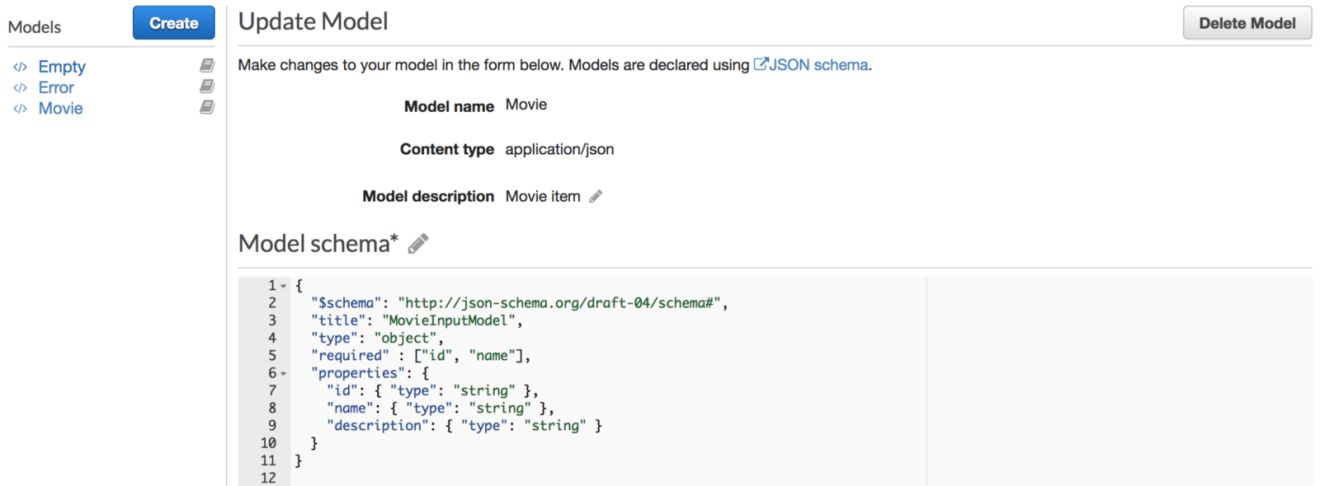
The model above defines a movie entity with 3 attributes and requires id and name attributes to be defined (used during validation).
Head back to “Resources” page and click on “Method Request” from the POST method, enable the request validator option as below:
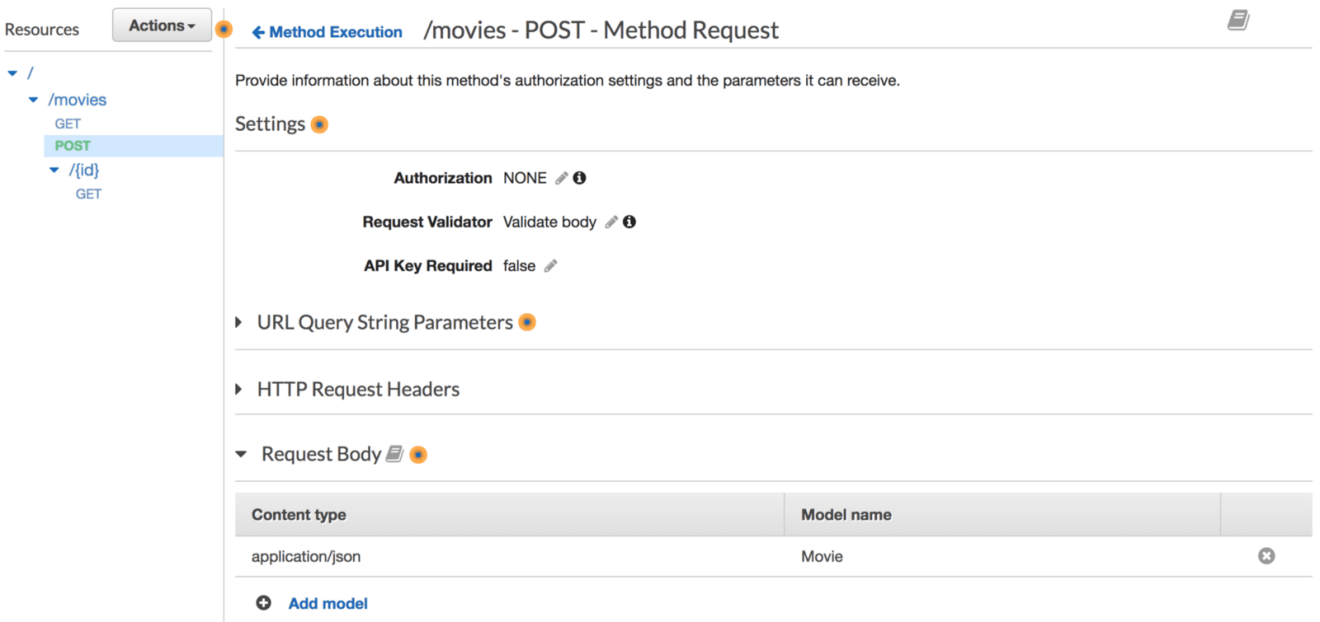
If you try to insert a new movie without providing the required parameters, a bad request message error will be returned:
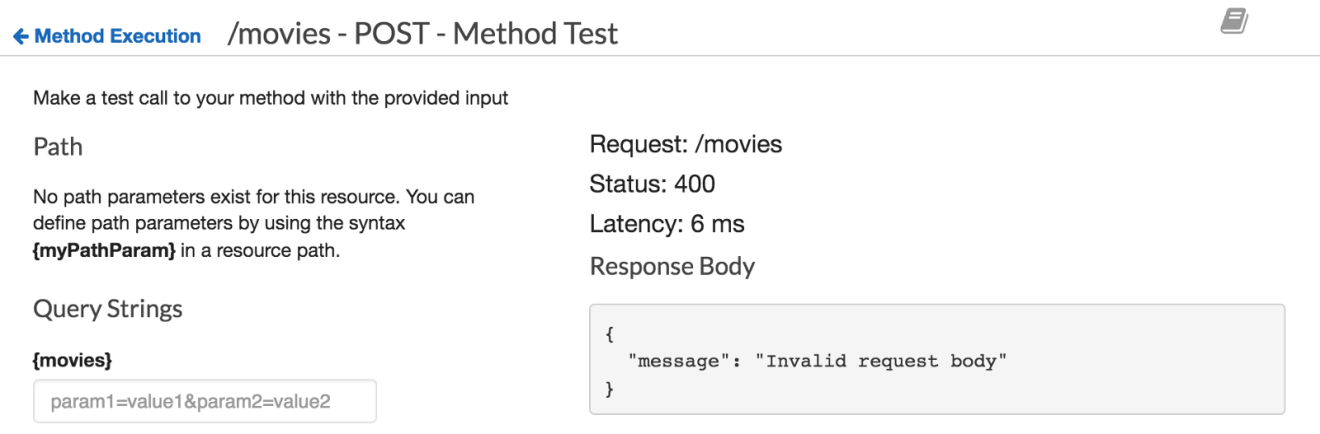
You can override the default 400 message from the “Gateway Responses” as follows:
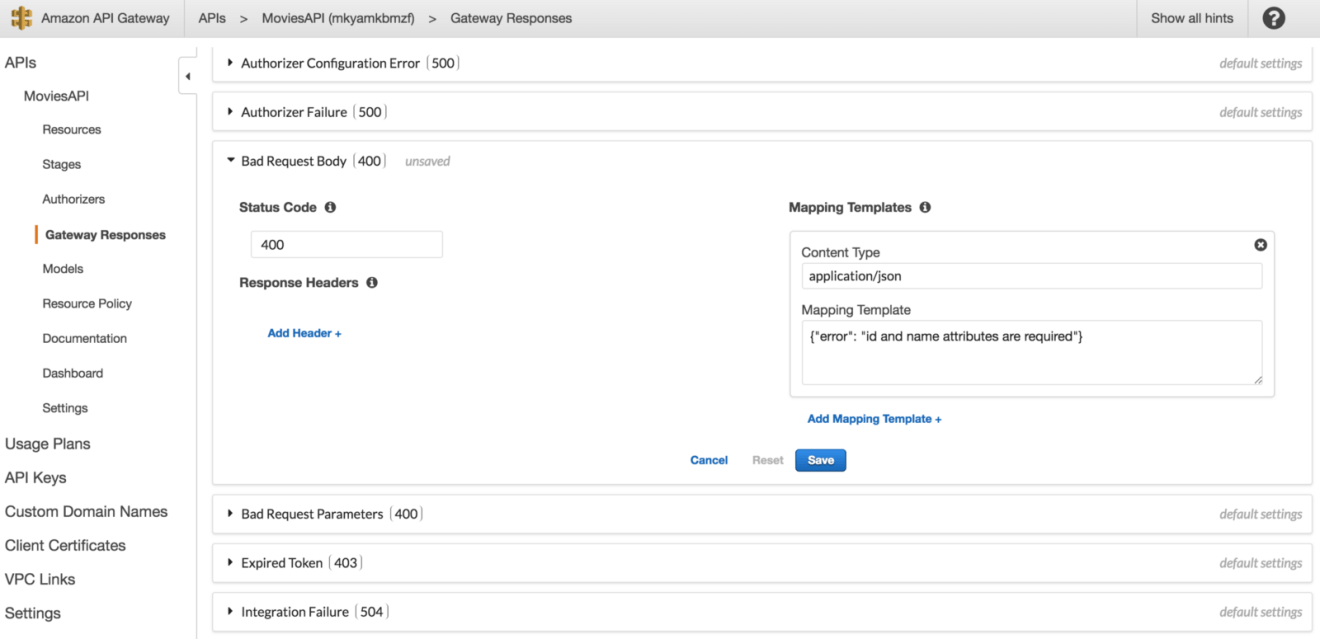
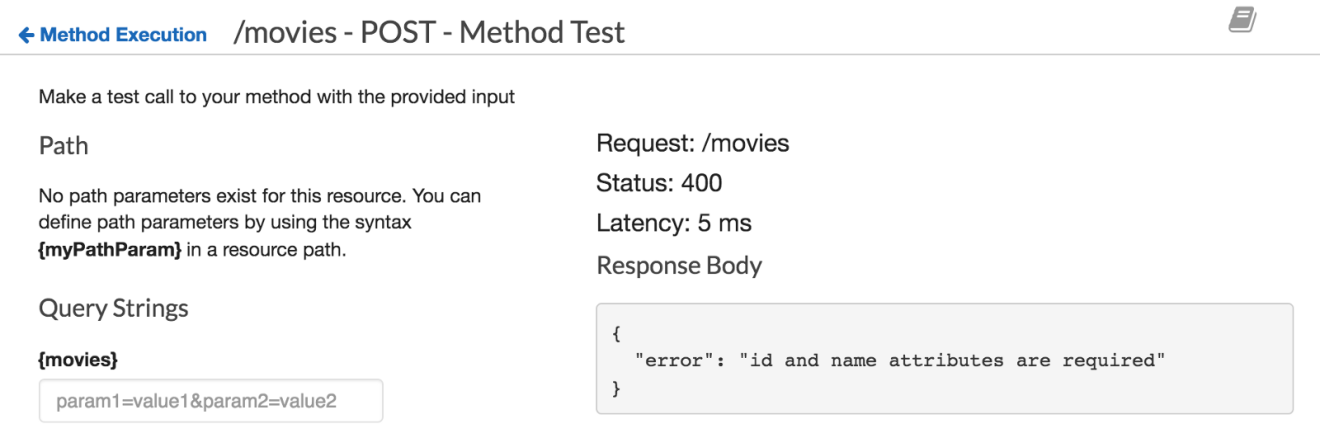
As a result, the user defined error message will be returned:
Great! Try implementing the PUT and DELETE methods:
Authentication
The serverless API that we have built so far works like a charms. However, its open to the public, anyone can insert data into DynamoDB table if he/she has the API Gateway invocation URL. Luckily, API Gateway offers two ways to handle authentication:
API Gateway Authentication with Cognito and Lambda Authorizer
AMAZON COGNITO
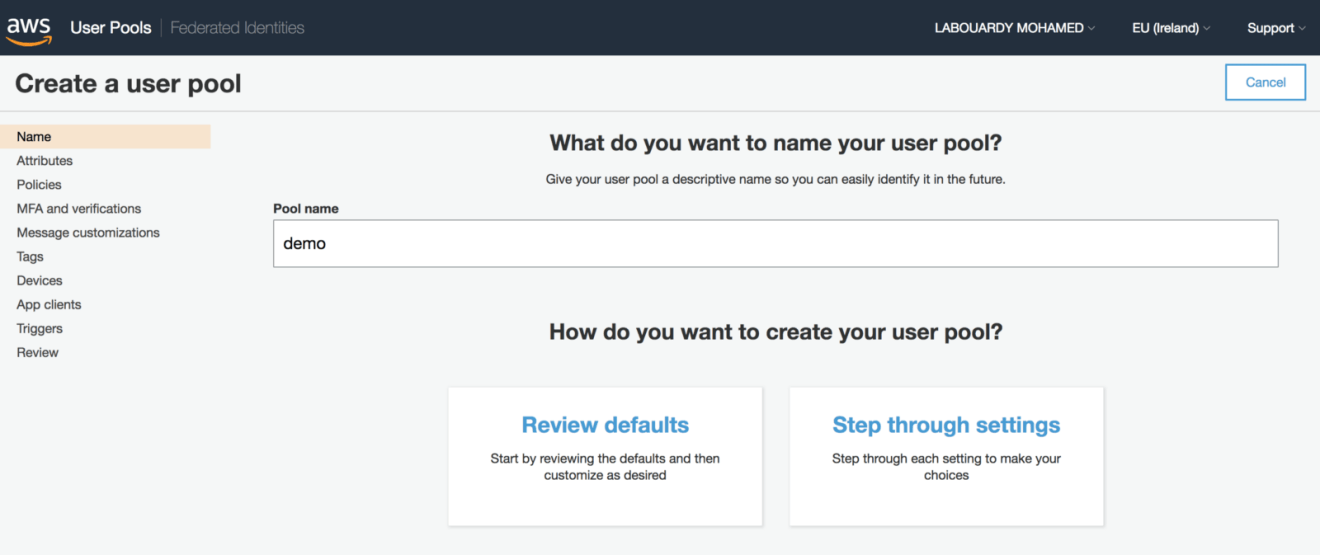
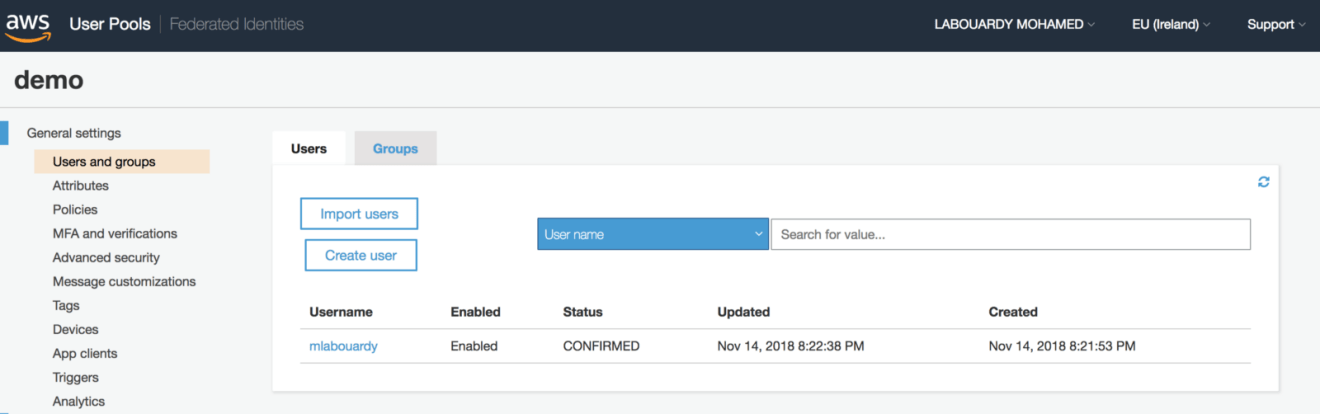
Create a new user pool, click on “Review defaults” to create a pool with default settings. A success message should be displayed at the end of the creation process:
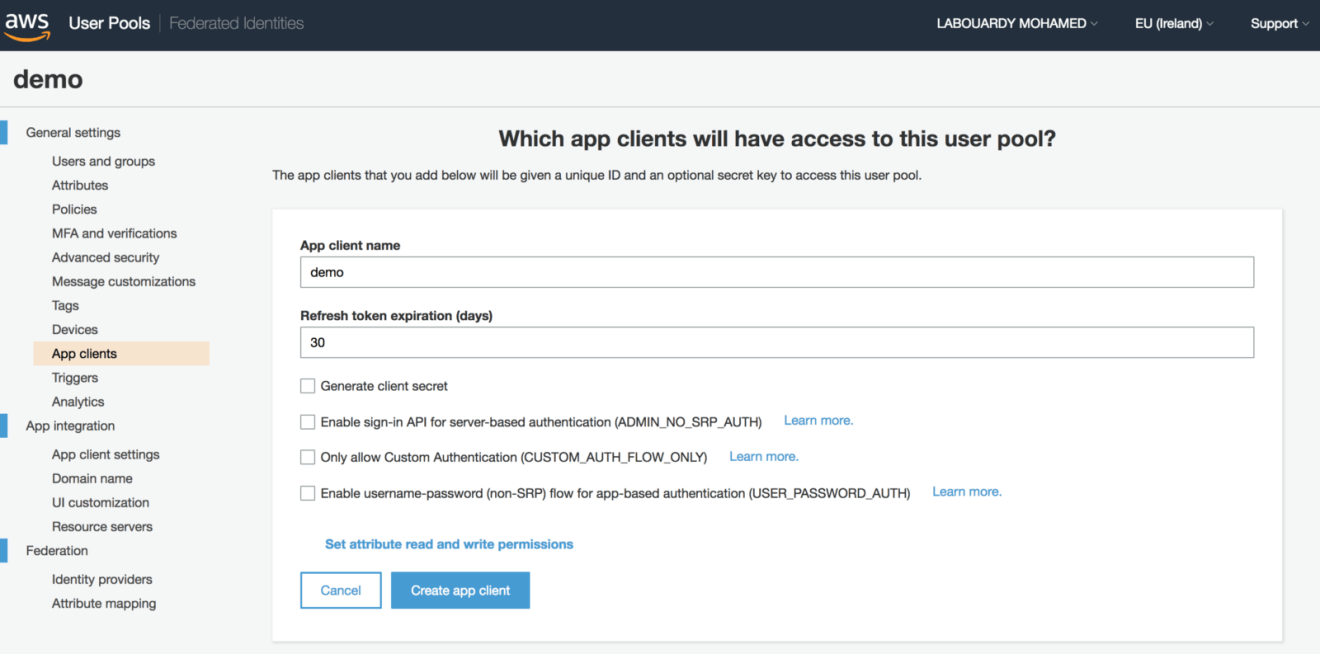
After creating your first user pool, register your serverless API from “App clients” under “General settings” and select “Add an app client”. Give the application a name and check the server-based authentication ADMIN_NO_SRP_AUTH option:
Create a new user using the AWS command line:
1 | # Create a user |
Now that the user pool has been created, we can configure the API Gateway to validate access tokens from a successful user pool authentication before granting access to DynamoDB.
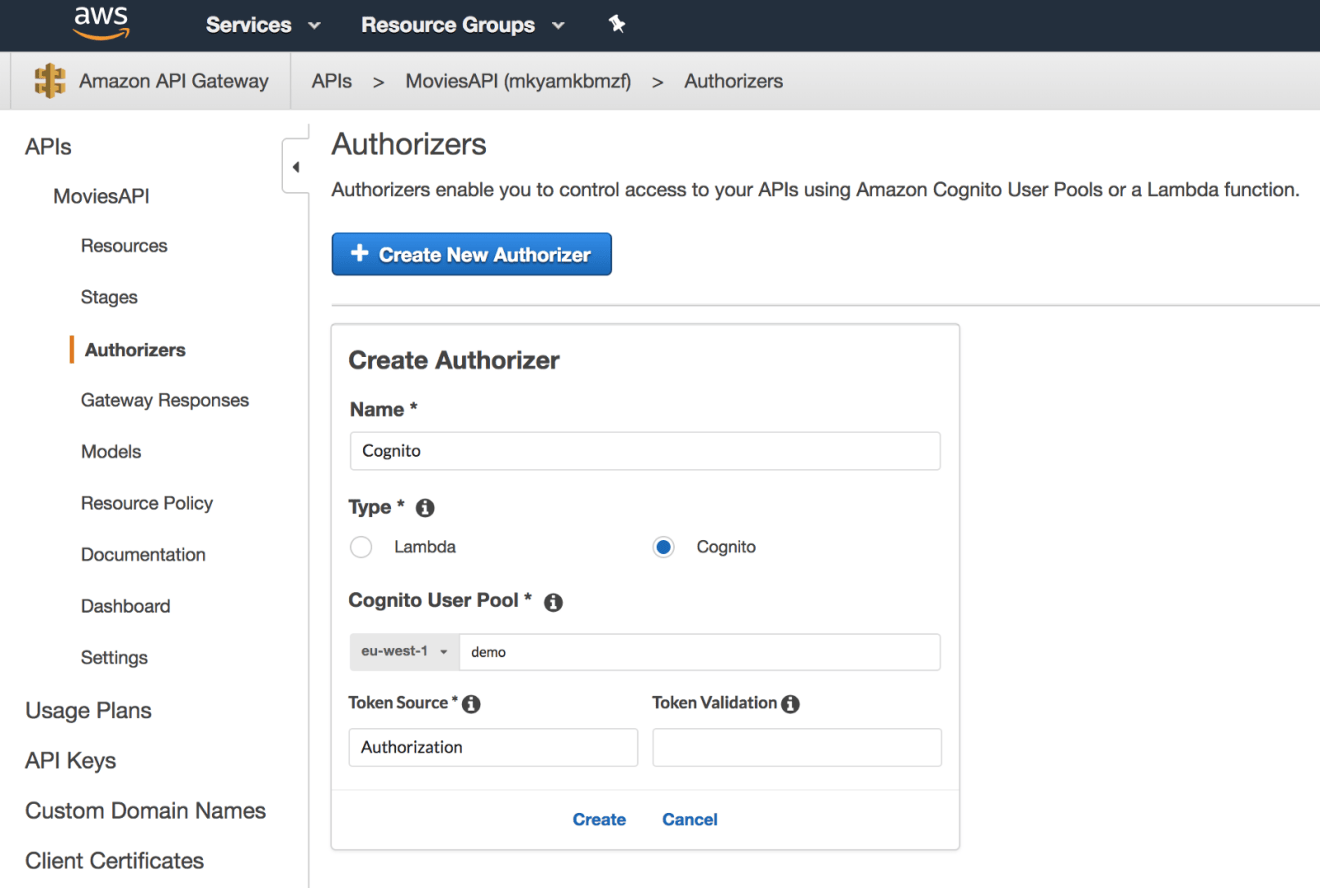
To begin securing API access, go to API Gateway console, choose the RESTful API that we built in the previously, and click on “Authorizers” from the navigation bar. Click on the “Create New Authorizer” button and select “Cognito”. Then, select the user pool that we created earlier and set the token source field to Authorization. This defines the name of the incoming request header containing the API caller’s identity token for Authorization:
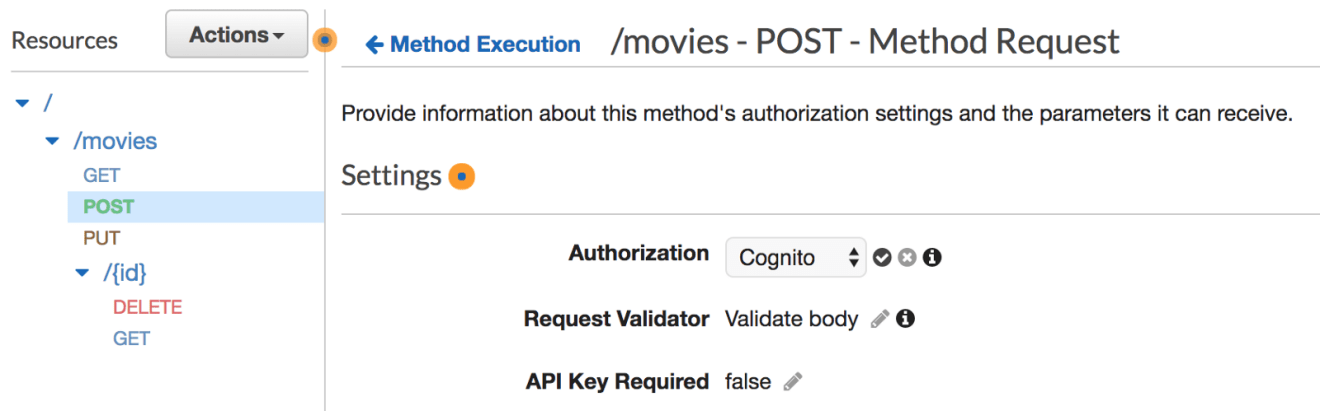
You can now secure all of the endpoints, for instance, in order to secure the endpoint responsible for creating an new movie. Click on the corresponding POST method under the /movies resource. Click on the “Method Request” box, then on “Authorization”, and select the user pool we created previously:
Once done, redeploy the API and try to insert a new movie using the API invocation URL. This time, the endpoint is secured and requires authentication:
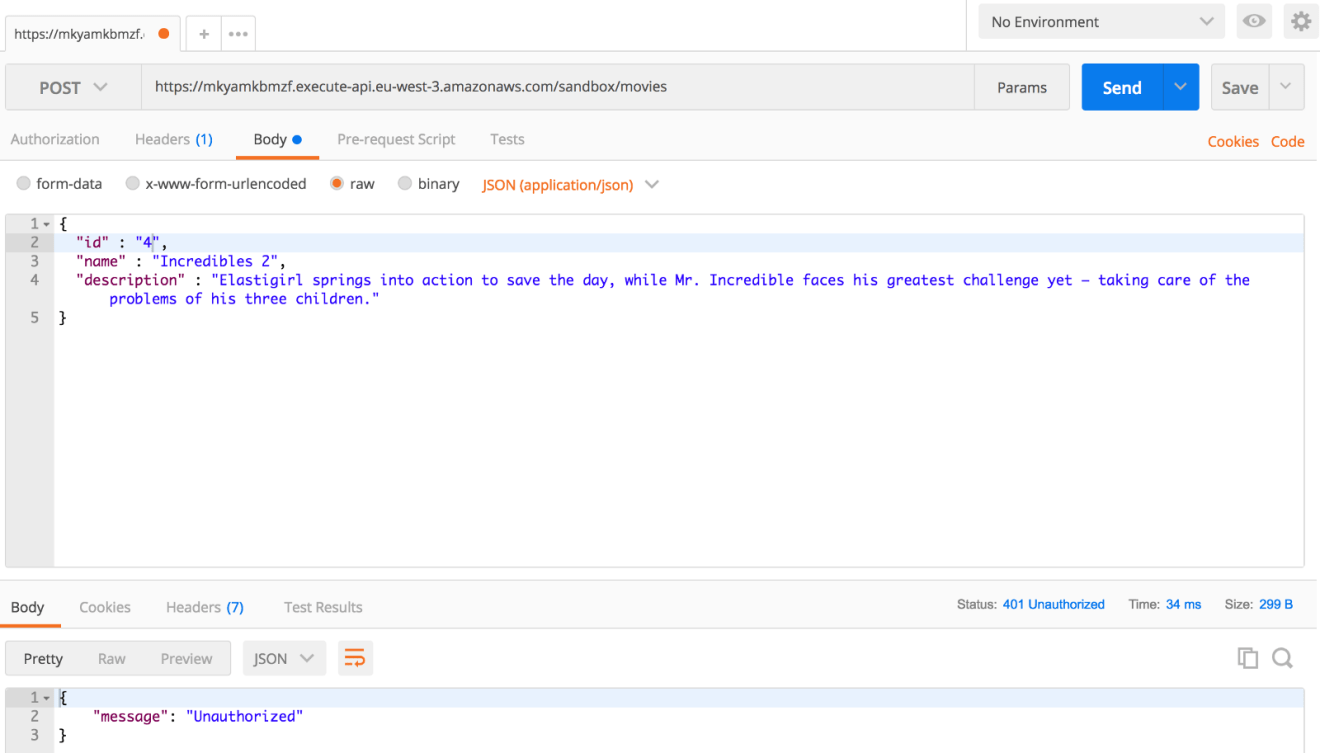
In order to authenticate, we need to obtain an identity token for the signed-in user from the the user pool and include the identity token in the Authorization header for the API Gateway requests. Issue the following AWS CLI command to get a new token:
1 | aws cognito-idp admin-initiate-auth -region AWS_REGION -cli-input-json file://input.json |
The command above takes a JSON file with the following attributes:
1 | { |
Once executed, the preceding command will return the following JSON response:
1 | { |
Copy the ID token and add it to the Authorization header of your request:
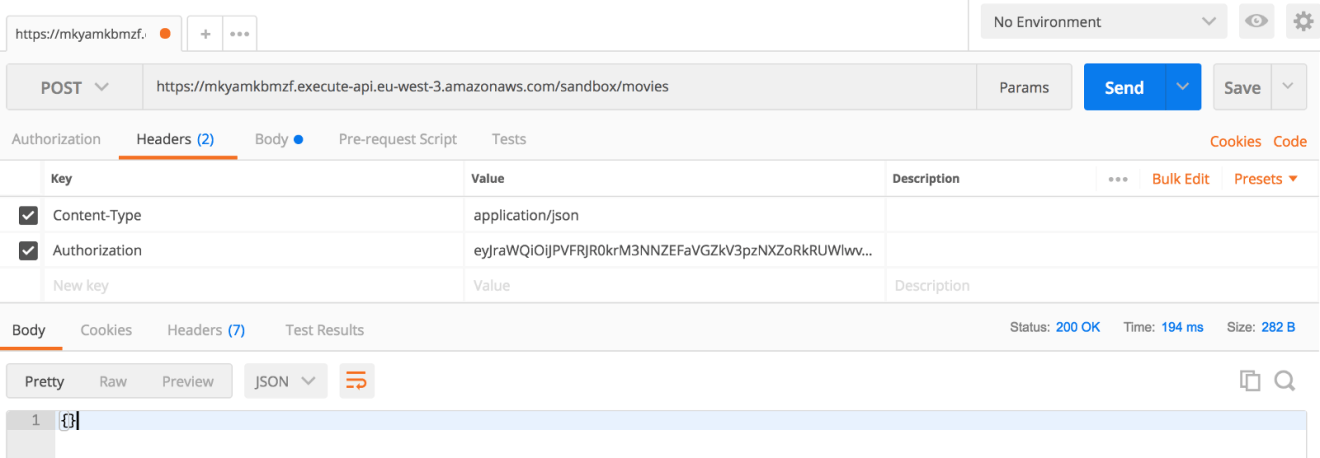
The API Gateway will verify the token and will invoke the PutItem operation on the movies table, which will insert a new movie into the table:
LAMBDA AUTHORIZER
When a client sends a request to your API, it will go through the API Gateway, which will extracts the token from the request and calls your Lambda function authorizer with it. The function evaluates the token, generates a policy and sends it back to API Gateway. API Gateway evaluates the policy and invoke the DynamoDB action registered for the API endpoint.
For the sake of simplicity, our function will verify if the token provided by the client equals to our secret (environment variable) and returns a policy document based on the result. The following is the function handler source code written in Node.JS:
1 | const TOKEN = process.env.TOKEN; |
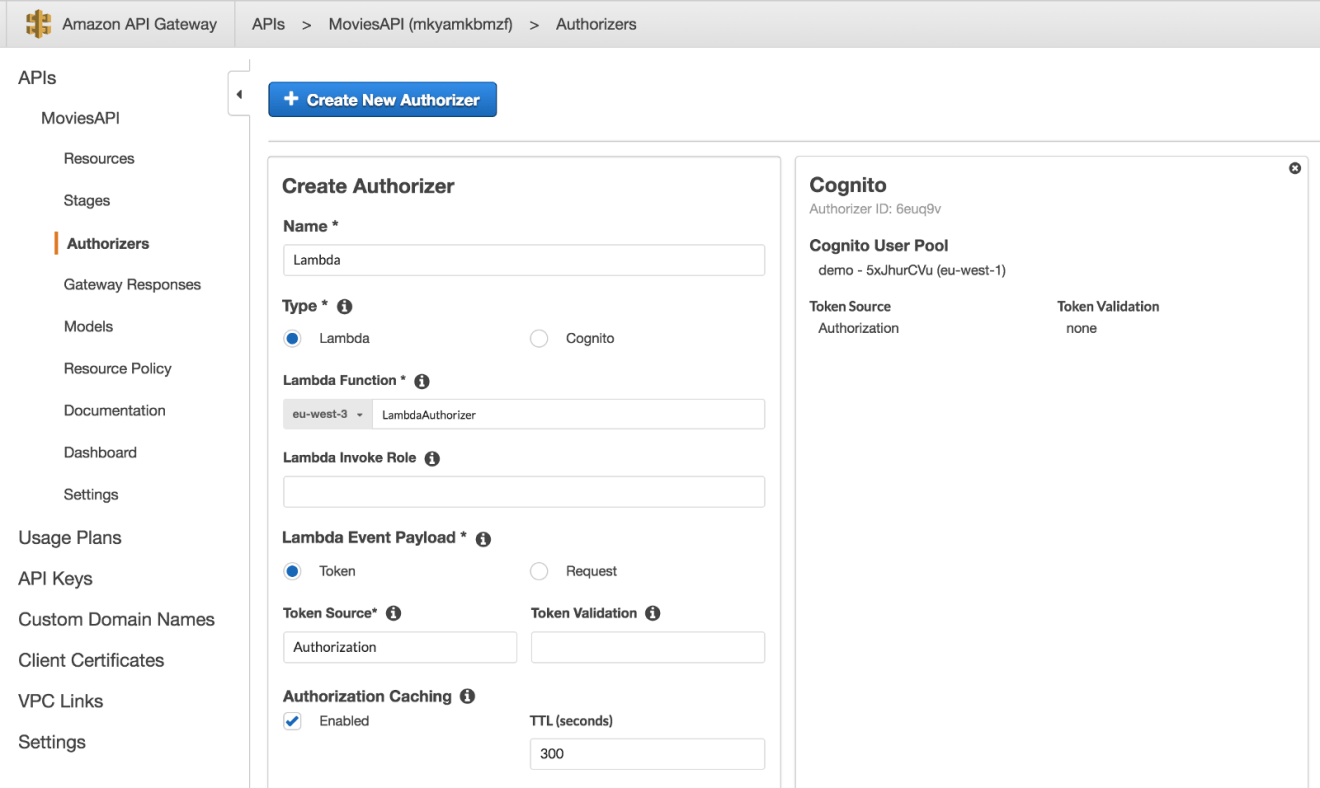
Head back to API Gateway and created a new “Lambda Authorizer” and set Authorization to be the header API Gateway will extract the token from:
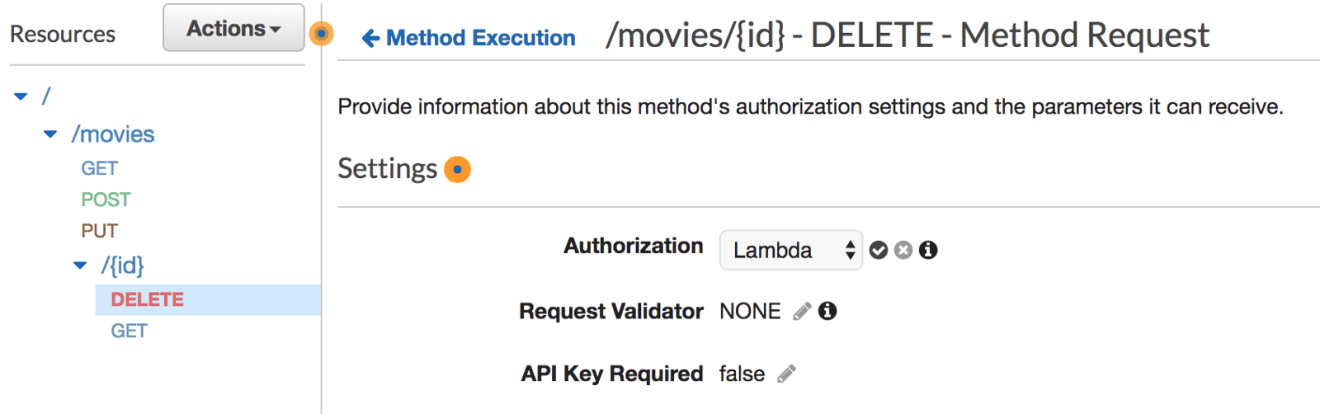
Choose the method you want to secure, let’s say, it will be the endpoint responsible of deleting a movie from the table. Click on “Method Request” and under Authorization select your new authorizer:
Let’s try calling the endpoint, As expected, we’re not getting through to our real endpoint:
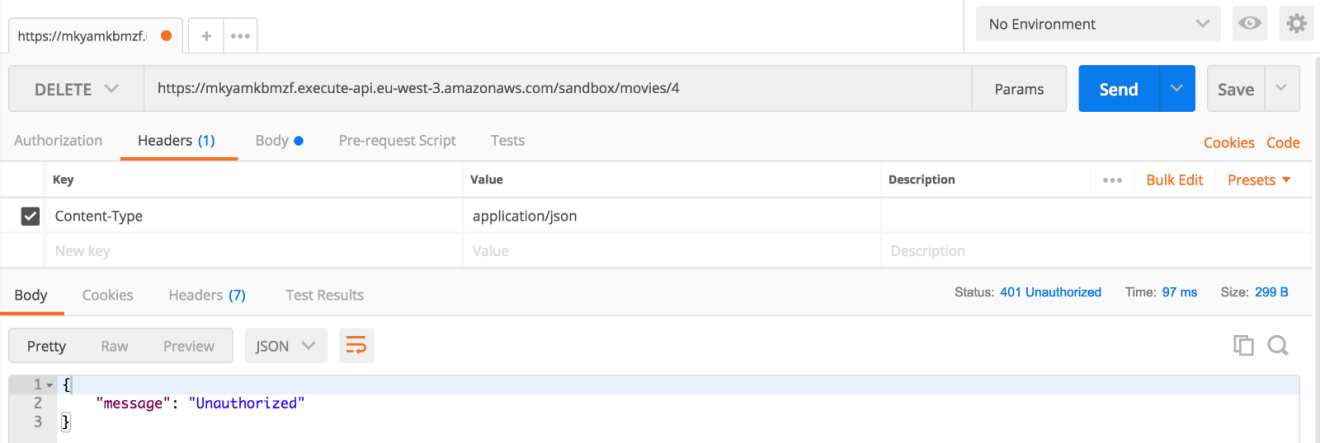
If you include the secret token to the Authorization header of your request, you should be able to delete an item:
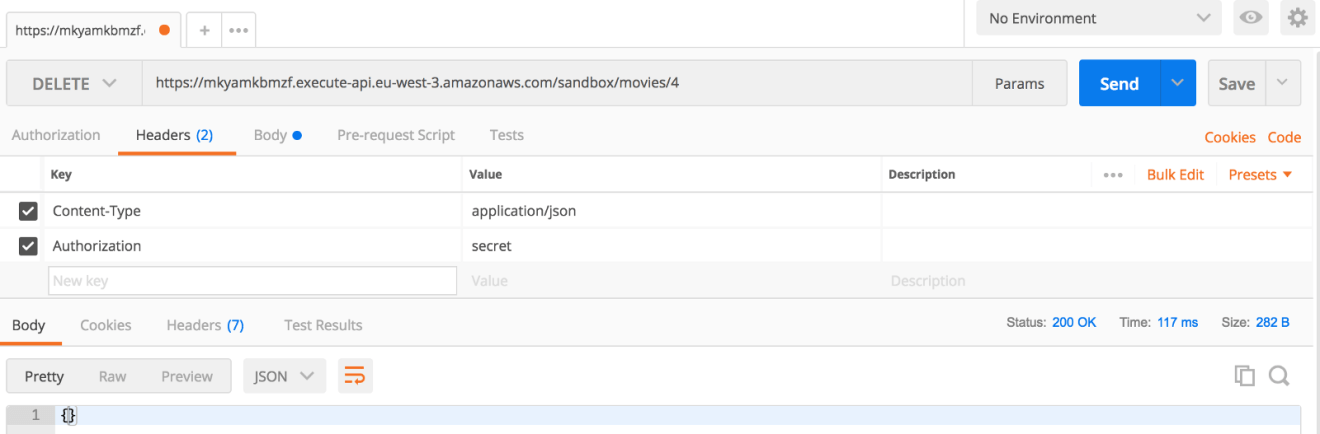
Looks good!
API Throttling
You can use usage plans combined with API keys to set method-level throttling limits for your API and define how much and how fast clients can access your API (request rates and quotas).
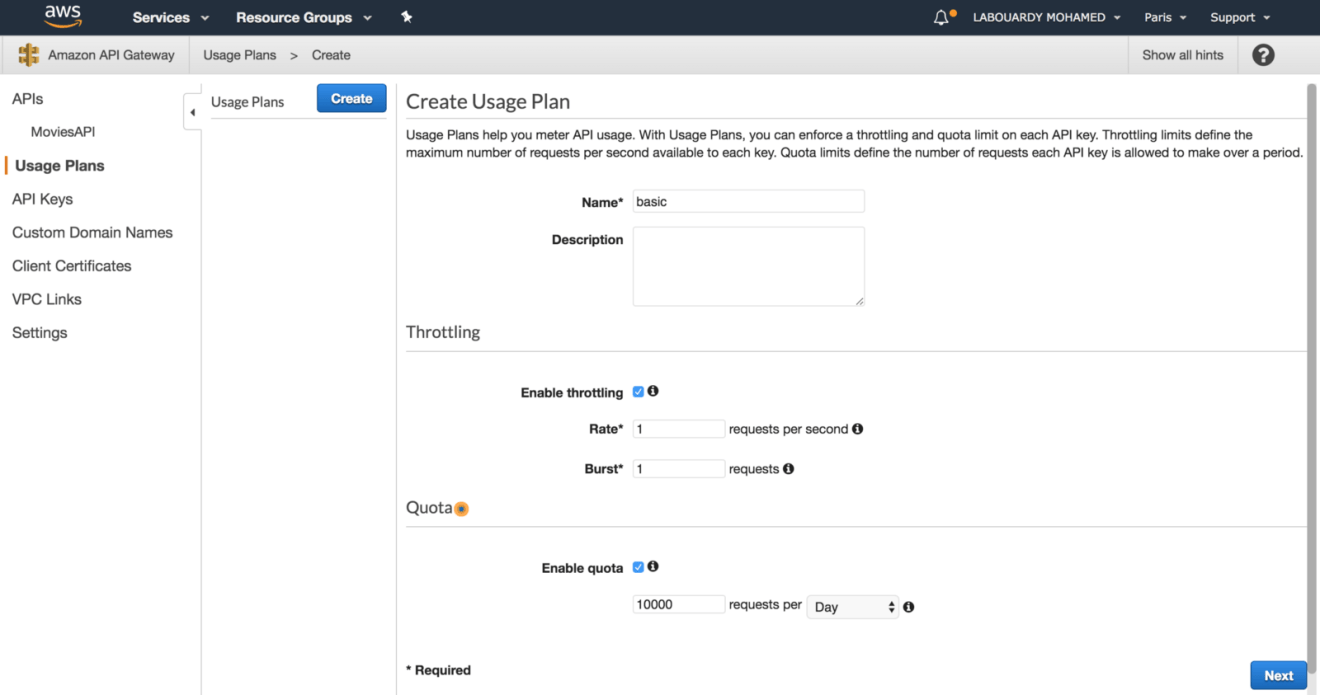
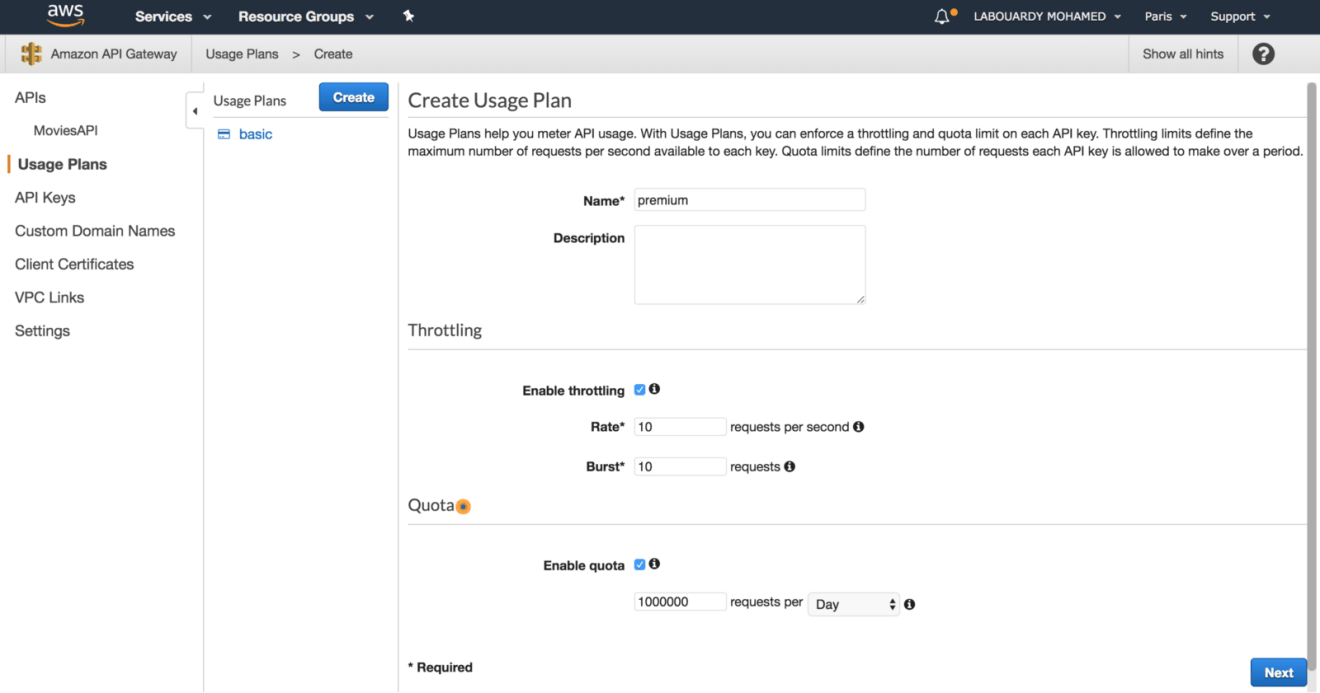
The following procedure describes how to create a usage plan:
API USAGE
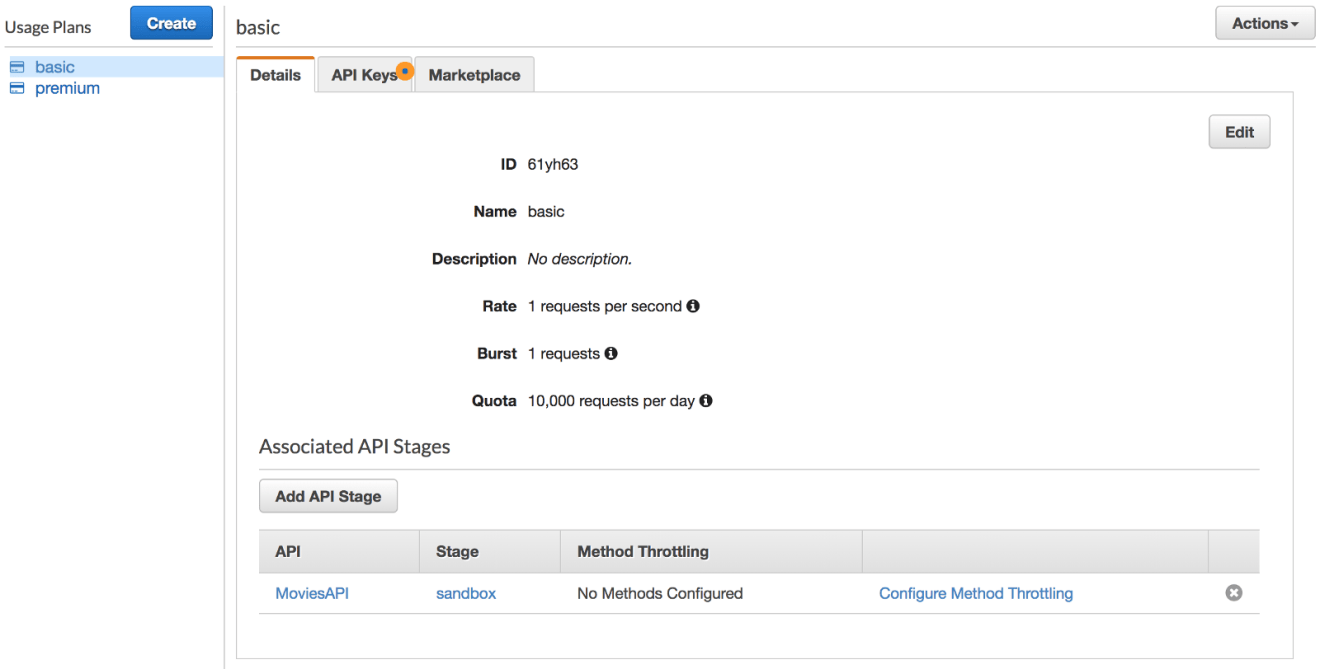
Create a usage plan called basic, with a throttling limit of 1 request per second and quota limit of 10000 requests per day:
Create a 2nd usage plan called premium, with a throlling limit of 10 requests per second and a quota limit of 1 million requests per day:
API KEYS
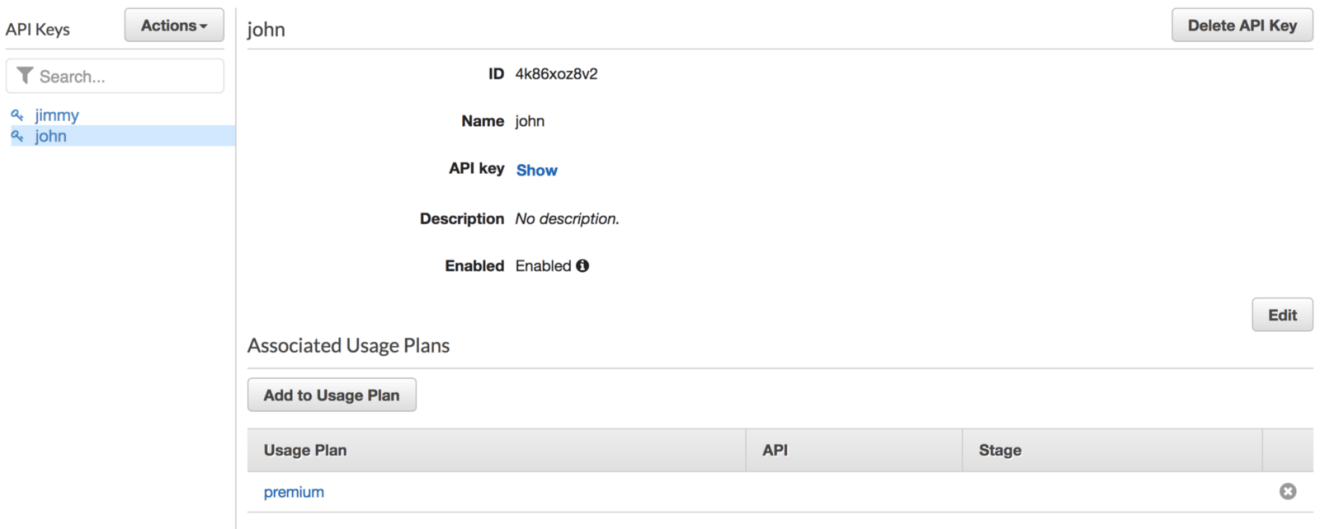
Next, create two API keys:
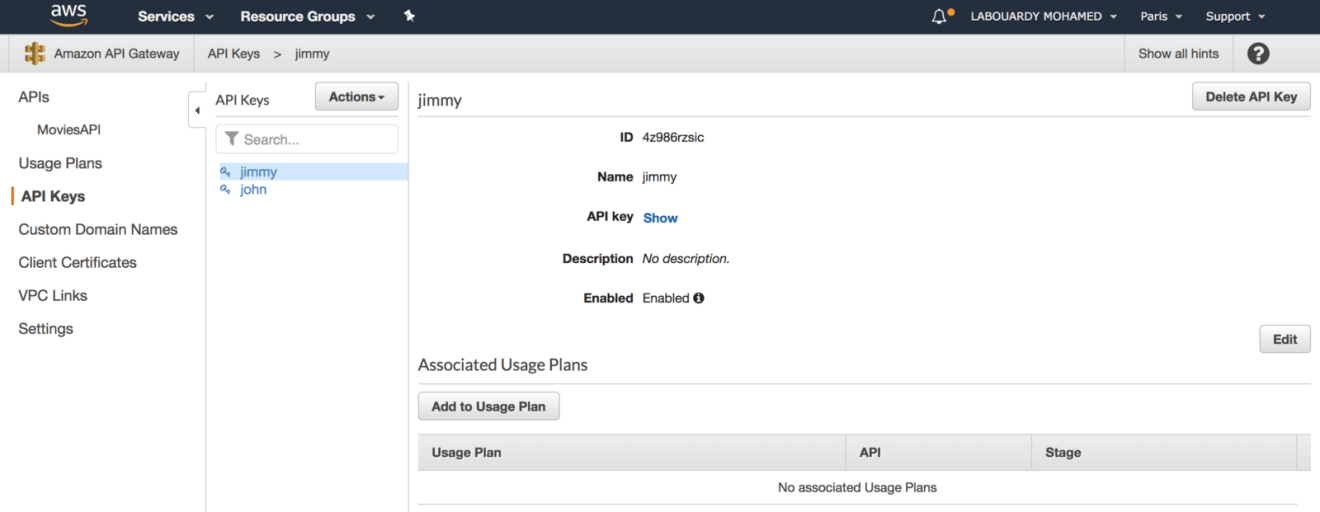
Assign the first API key to basic usage plan and second key to premium usage plan:
Associate the usage plans we created to the API deployment stage:
Configure an API method to require an API key:
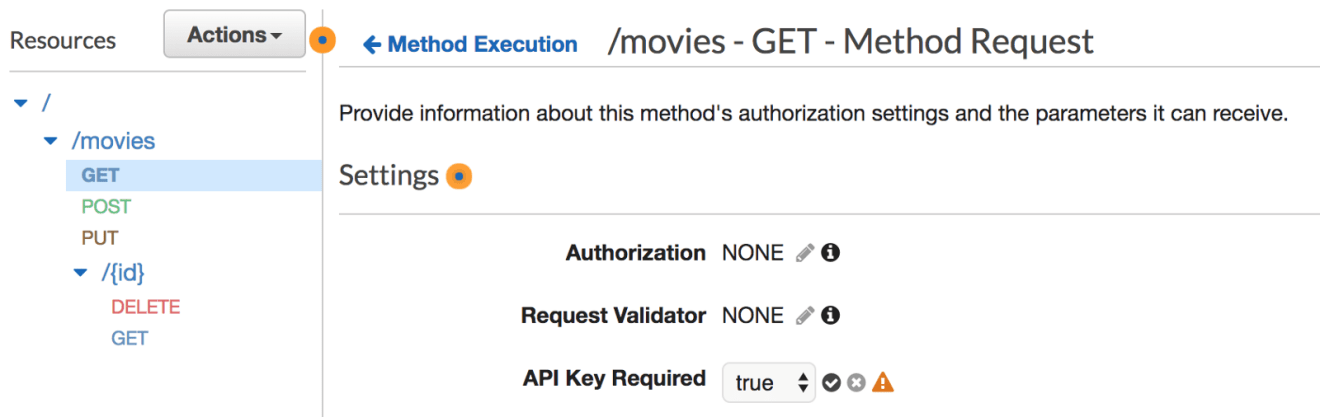
Deploy or redeploy the API for the requirement to take effect:
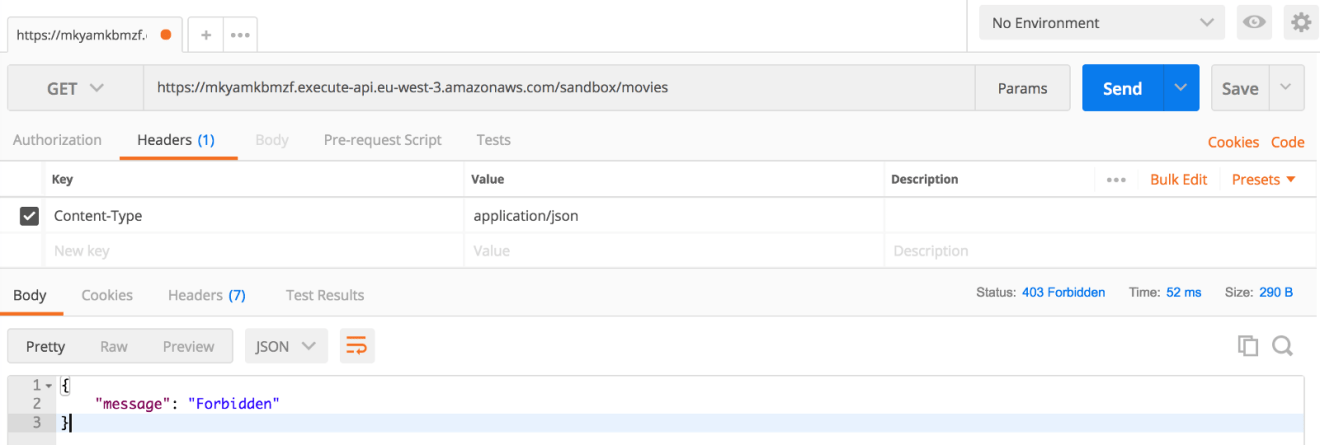
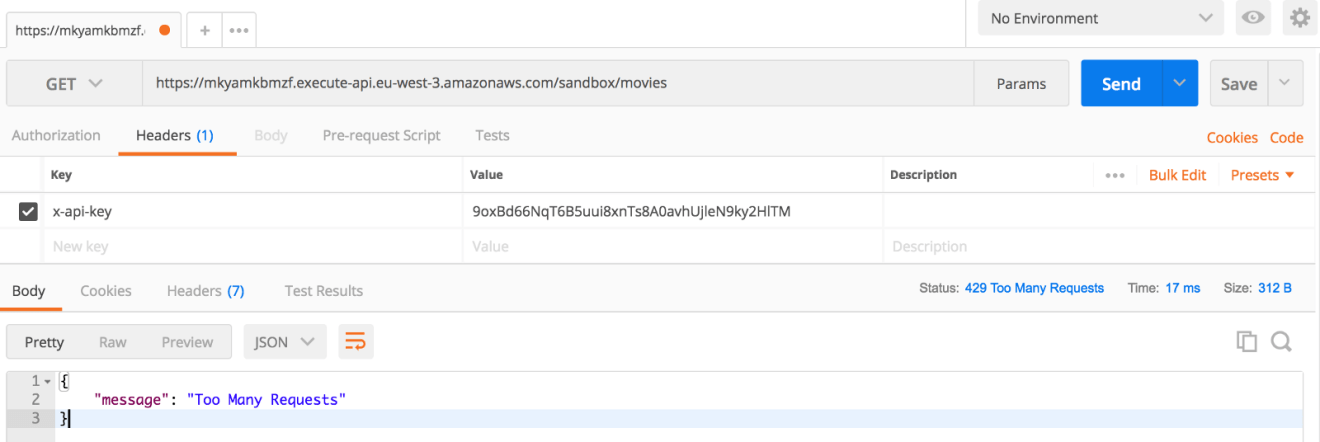
Now if you added the x-api-key header. If all goes well you will receive output like this:
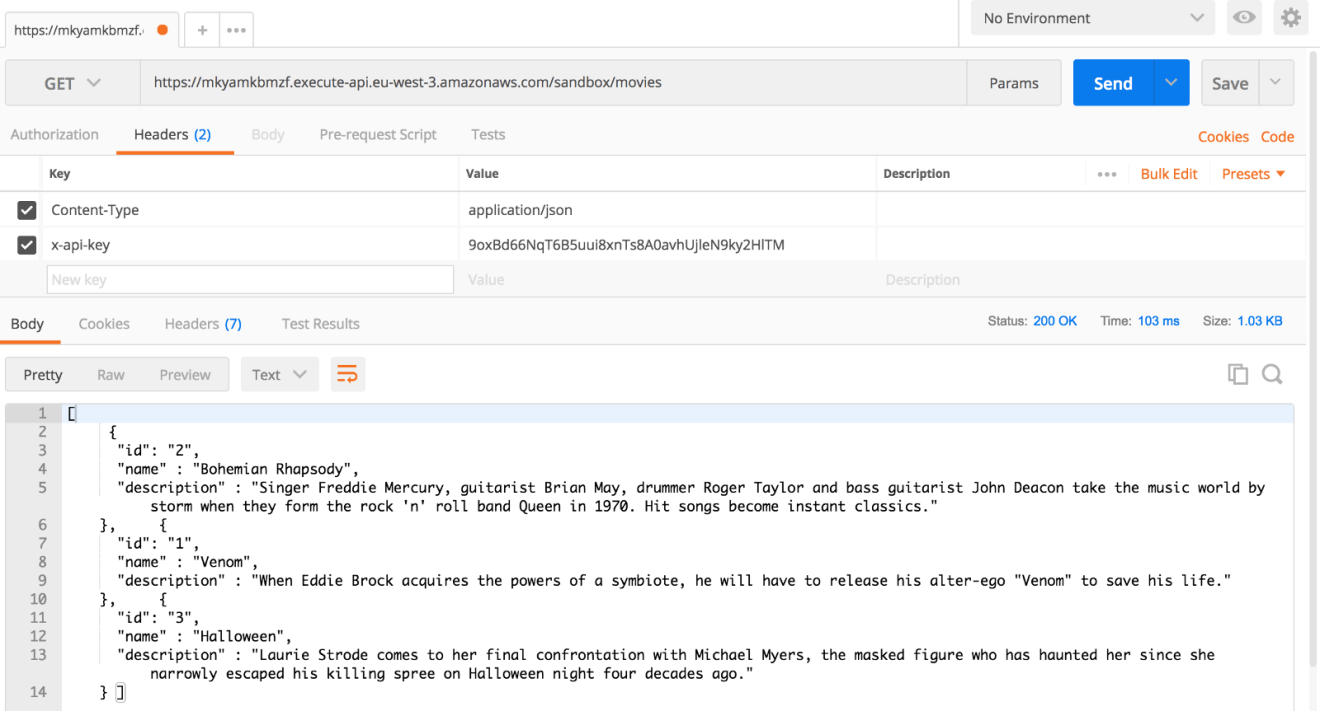
If you exceed the rate limit or quota limit associated with your API key, a “Too many requests” HTTP error will be returned:
Custom Domains
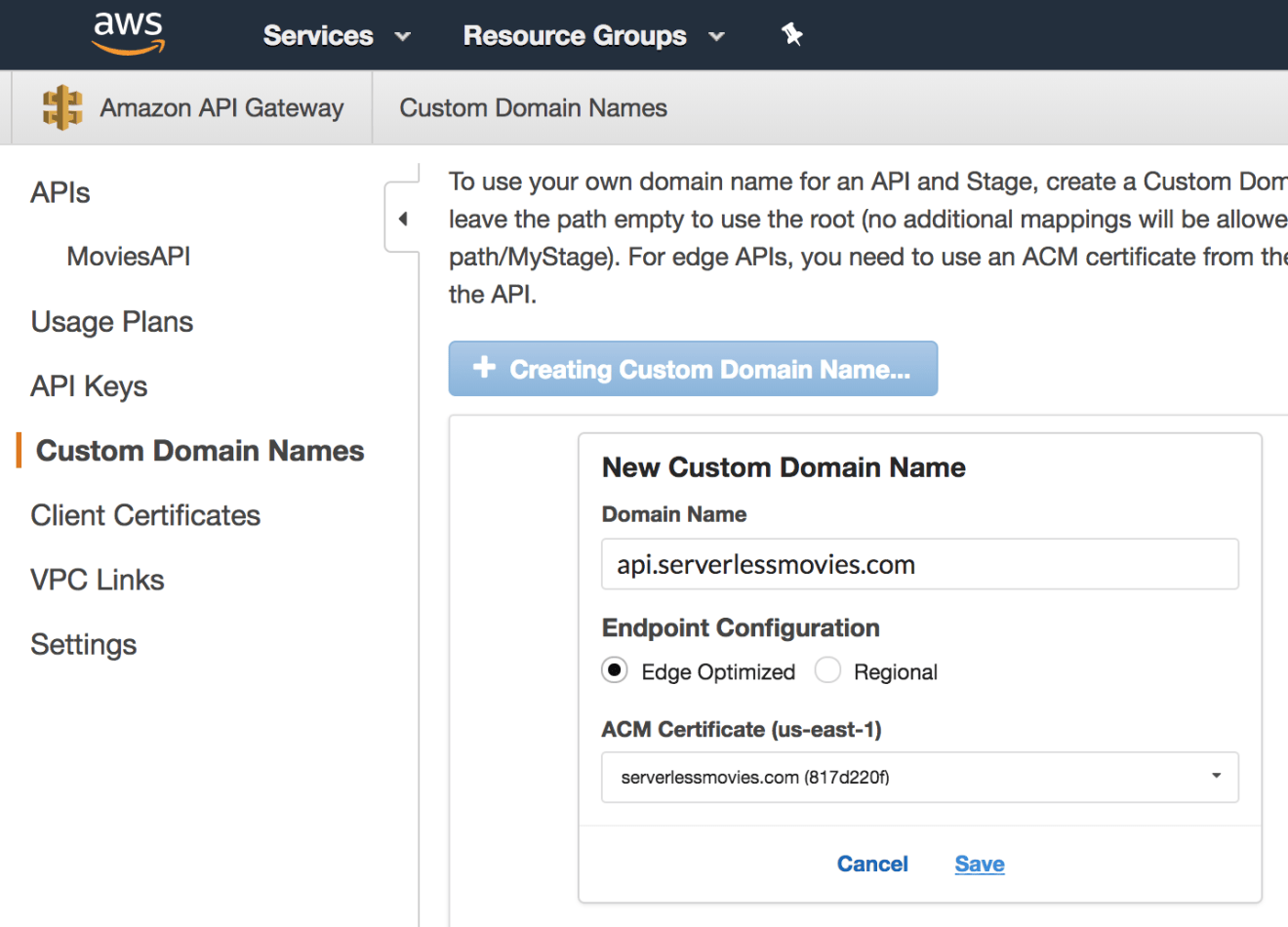
You can use your own domain name for an API and deployment stage, create a Custom Domain Name backed by an ACM (Amazon Certificate Manager) certificate:
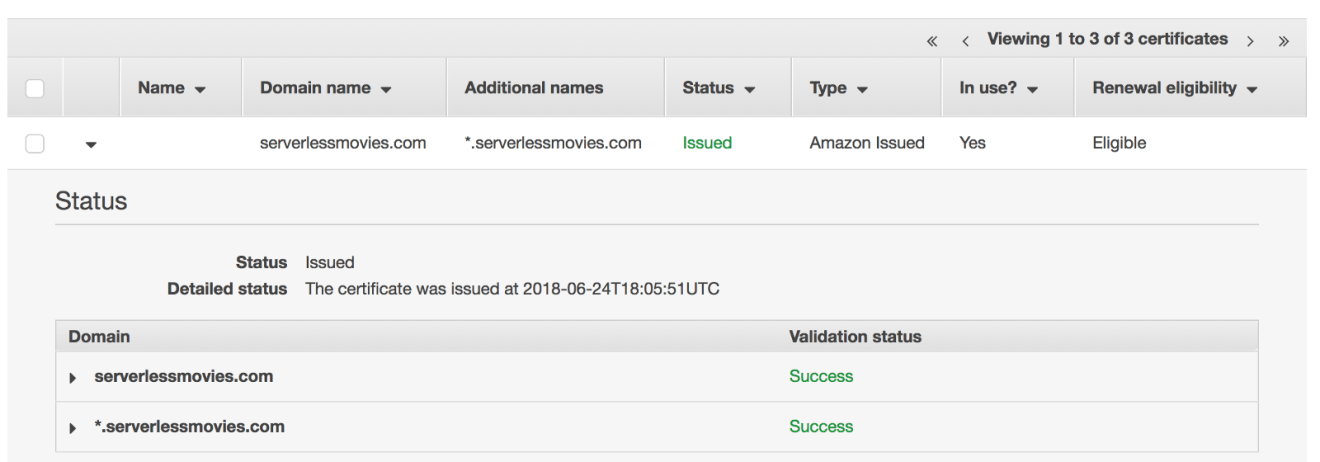
Create a new custom domain name from API Gateway Console:
Add a path mapping to map your domain name to your API deployment stage:
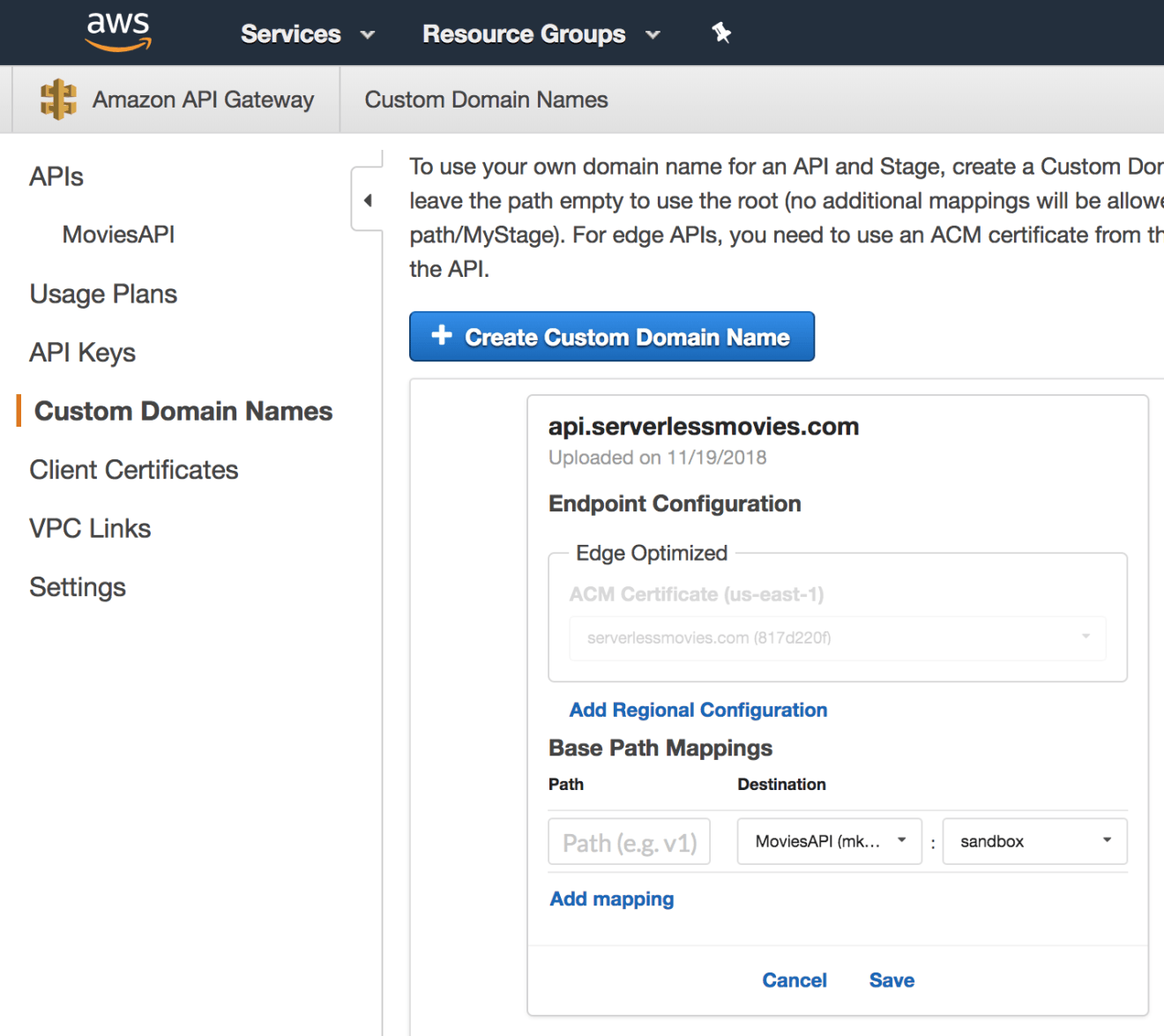
Once configured, you can query your API using your custom domain name as follows: https://api.serverlessmovies.com/movies
Documentation
Before finishing this guide, we will go through how to create documentation for the serverless API we’ve built so far.
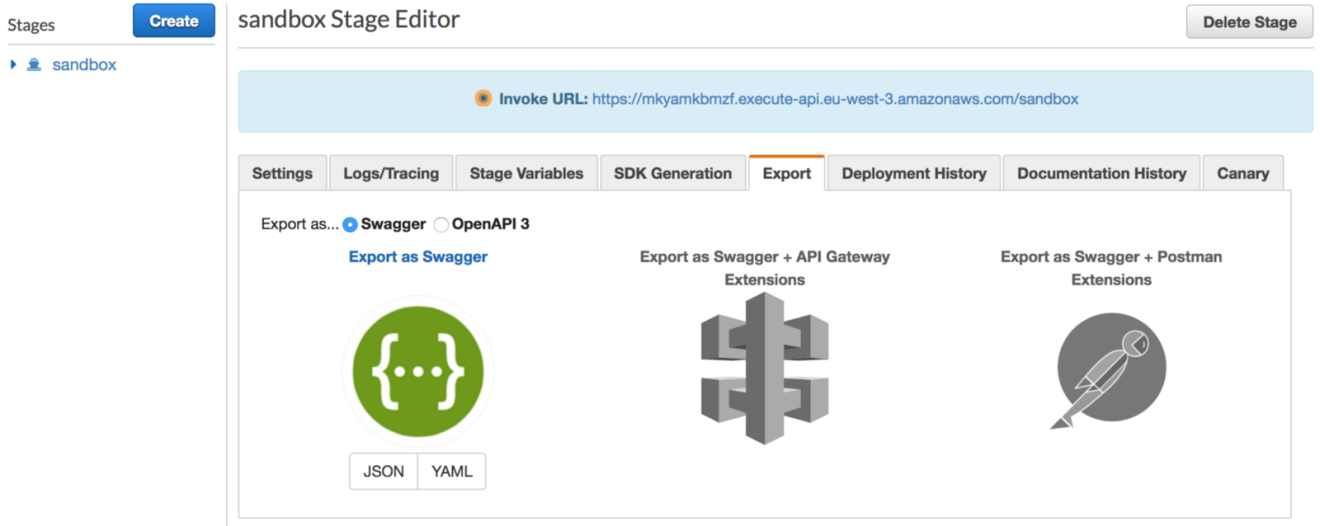
On the API Gateway console, select the deployment stage that you’re interested in generating documentation for. In the following example, I chose the sandbox environment. Then, click on the Export tab and click on the Export as Swagger section:
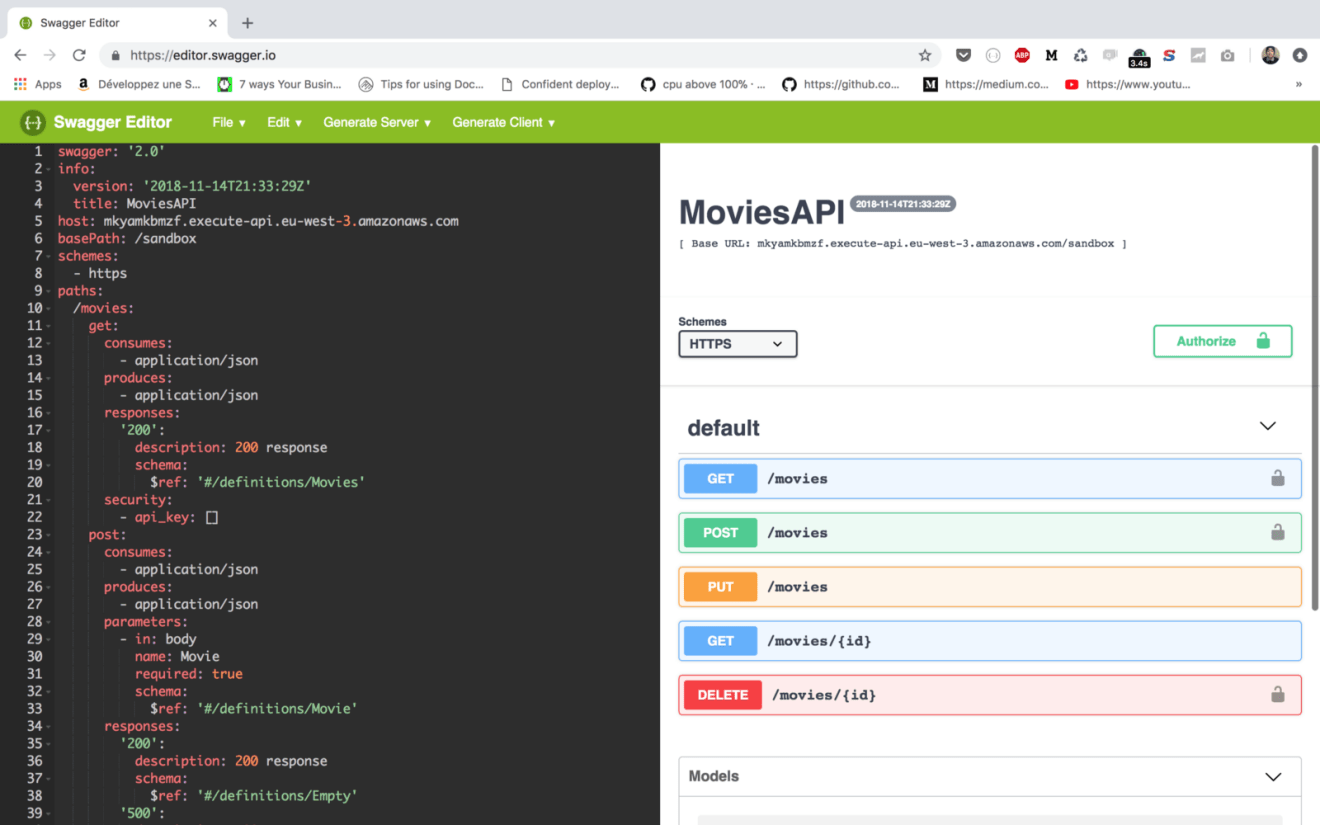
Swagger is an implementation of the OpenAPI, which is a standard defined by the Linux Foundation on how to describe and define APIs. This definition is called the OpenAPI specification document.
You can save the document in either a JSON or YAML file. Then, navigate to https://editor.swagger.io/ and paste the content on the website editor, it will be compiled and an HTML page will be generated as follows:
Like what you’re reading? Check out my book and learn how to build, secure, deploy and manage production-ready Serverless applications in Golang with AWS Lambda.
Drop your comments, feedback, or suggestions below — or connect with me directly on Twitter @mlabouardy.